KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The immensely popular children’s online playground Animal Jam has suffered a data breach impacting 46 million accounts.
Animal Jam is a virtual world created by WildWorks, where kids can play online games with other members. Geared towards children ages 7 through 11, Animal Jam has over 300 million animal avatars created by kids, with a new player registering every 1.4 seconds.
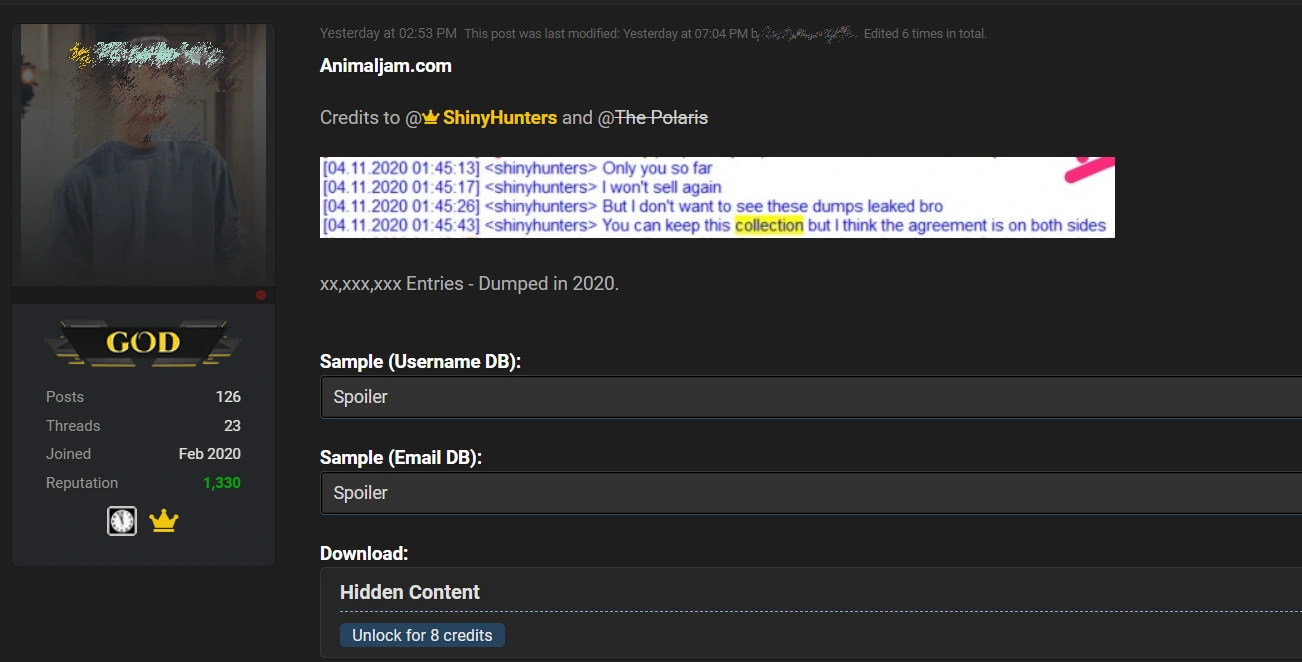
Yesterday, a threat actor shared two databases belonging to Animal Jam for free on a hacker forum that they stated were obtained by ShinyHunters, a well-known website hacker.
The two stolen databases are titled ‘game_accounts’ and ‘users’ and contain approximately 46 million stolen user records.
As part of the free release, the threat actor shared only a partial database containing approximately 7 million user records for children/parents who signed up for the game.
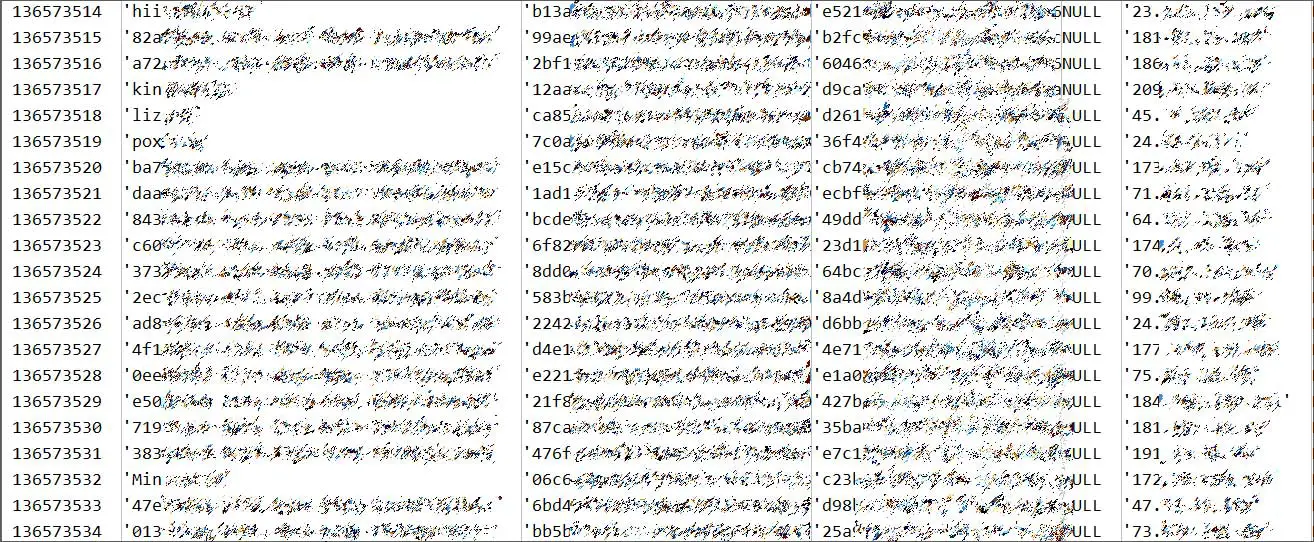
Based on the timestamps on the sample records seen by BleepingComputer, the database was likely stolen on October 12th, 2020.
In what should be considered a model on transparent reporting of a data breach, WildWorks shared with BleepingComputer that they learned of the breach this morning and have been actively investigating it.
Also Read: Letter of Consent MOM: Getting the Details Right
WildWorks CEO Clary Stacey told BleepingComputer that he believes the threat actors obtained WildWork’s AWS key after compromising the company’s Slack server. When the breach occurred, it was quickly addressed, but they were unaware that any data was stolen at the time.
After learning today of the stolen database, their investigation revealed that the threat actors gained access to databases that contained:
Though the amount of records stolen is quite large, Stacey states it is a small subset of the total number of Animal Jam users accounts registered since 2010. Animal Jam now has over 130 million registered players and 3.3 million monthly active users.
Stacey stated that they are preparing a report for the FBI Cyber Task Force and notifying all affected emails. They will also be making a public announcement that will link to a FAQ on their site.
“WildWorks is a small company, but we take player security very seriously. We are deeply concerned to learn of this breach, albeit relieved that no sensitive information such as plaintext passwords or real names of children were exposed in this theft. ” Stacey shared with BleepingComputer.
WildWorks told BleepingComputer that they would continue to be transparent about the exposed data, and if any new information is learned from their investigation, it will be disclosed.
Also Read: A Look at the Risk Assessment Form Singapore Government Requires
If you or your child is an Animal Jam user, you should immediately change the account’s password.
If that password is used at any other site, it should also be changed to a unique password.
Using unique passwords at every site you have an account prevents a data breach at one site from affecting you at other websites you use.
It is also an excellent time to introduce your child to a password manager so that they get into the habit of using unique and robust passwords at every site they use. This practice will save them a lot of headaches in the future.
As this data can be used in targeted phishing attacks targeted at children, it is also essential to monitor your kid’s accounts for suspicious email.