KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The US Department of Justice has indicted a hacker known as ‘Fxmsp’ for hacking into and selling access to over three hundred organizations worldwide.
In an indictment unsealed today, the DOJ is charging a citizen of Kazakhstan named Andrey Turchin, also known as “Fxmsp,” with conspiracy to commit computer hacking, two counts of computer fraud and abuse (hacking), conspiracy to commit wire fraud, and access device fraud.
While the indictment and DOJ press release does not state if Turchin was arrested, BleepingComputer has been told by sources familiar with the case that local authorities detained him in Kazakhstan.
According to the indictment, Turchin would gain access to private networks through phishing attacks and brute-forcing the passwords of exposed remote desktop servers.
Once a network was breached, Turchin allegedly deployed password-stealing Trojans and remote access trojans (RATs) to harvest credentials and gain persistence in the system.
“TURCHIN and his accomplices perpetrated an ambitious hacking enterprise broadly targeting hundreds of victims across six continents, including more than 30 in the United States. Widely known in hacking circles by the moniker “Fxmsp,” TURCHIN employed a collection of hacking techniques and malicious software (malware) to gain and maintain access to victim networks,” a DOJ press release stated.
Under the alias ‘Fxmsp’, Turchin would then sell access to these networks on hacker forums and dark web marketplaces for prices typically ranging between $1,000 to tens of thousands, with some systems being sold for over $100,000.

Other threat actors would use these sold networks to deploy ransomware, steal data, or perform other malicious behavior.
Also read: 9 Policies For Security Procedures Examples
In May 2019, BleepingComputer exclusively reported that Fxmsp was selling stolen source code and access to major US antivirus companies’ networks.
Based on information shared with BleepingComputer by cyber intelligence firm Advanced Intel, Fxmsp conducted a hacking campaign in 2019 where he claimed to have breached Trend Micro, Symantec, and McAfee,
As part of this breach, Fxmsp claims to have stolen source code from all three vendors, with access to over 30TB of data from Trend Micro.
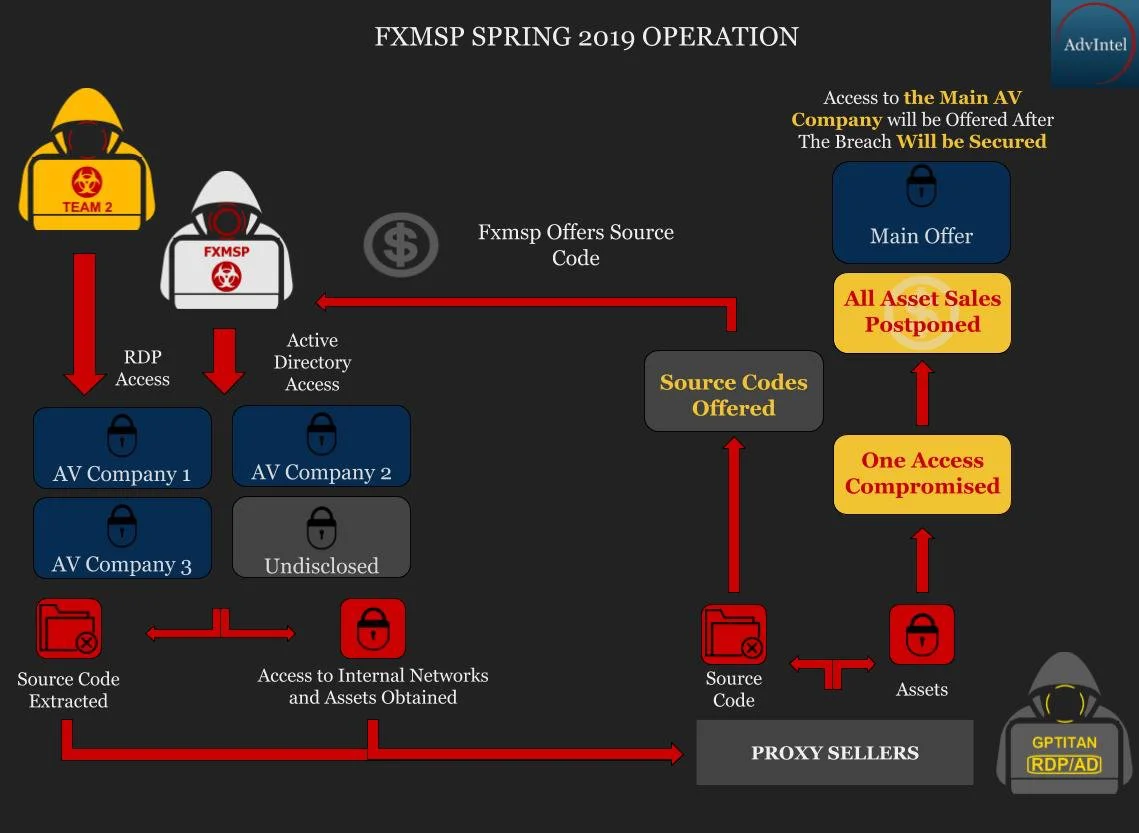
Access to these networks and the source code was being sold for $300,000 per vendor.
At the time, Symantec had told BleepingComputer that they were confident that they were not breached, Trend Micro states it was just a testing lab that was hacked, and McAfee said they were investigating the threat.
In addition to the AV vendors, Fxmsp had claimed to have access to a diverse host of victims, including businesses in the manufacturing, energy, financial, government, air transport, food, and education verticals.
Also read: 7 Client Data Protection Tips to Keep Customers Safe