KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






An unauthenticated API call vulnerability in DPD Group’s package tracking system could have been exploited to access the personally identifiable details of its clients.
DPD Group is a parcel delivery service with a global presence, shipping around two billion parcels annually worldwide.
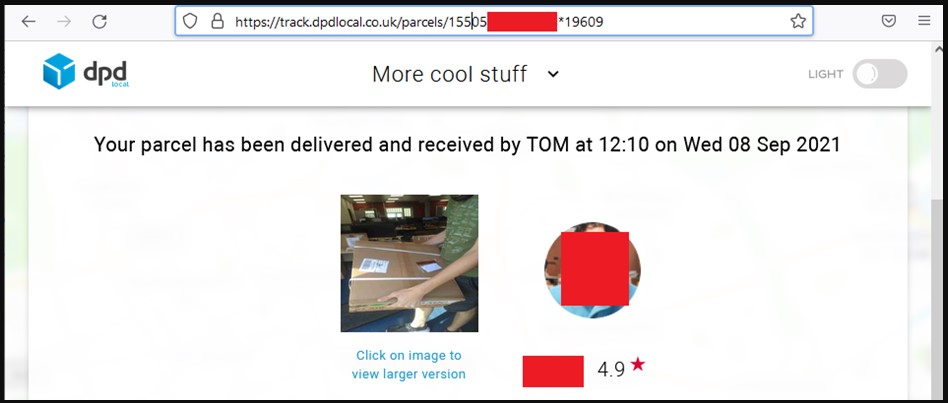
To track the status and position of their parcel, customers are expected to enter a parcel code and postcode, and if they match a valid entry in the database, they are authorized to view the shipping details.
Also Read: A guide to Singapore’s Do Not Call Registry
Researchers at Pen Test Partners explored the system and found that they could try out parcel codes on API calls and get back OpenStreetMap addresses with the recipient’s position on the map.
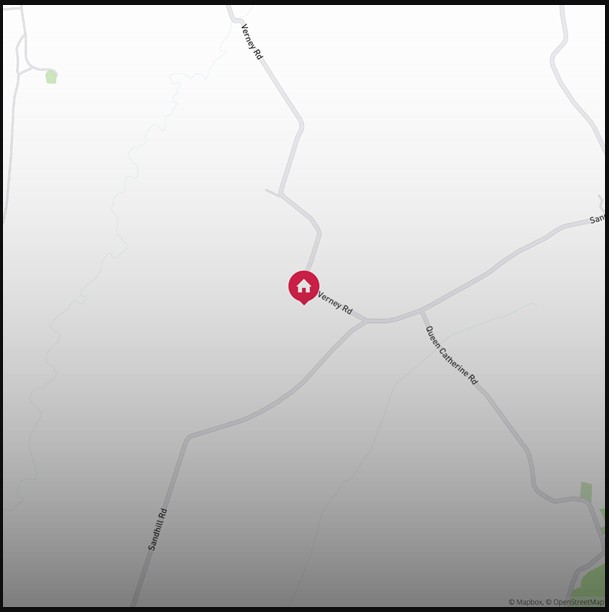
Although the call returned just a screenshot of the map, it is fairly easy to derive the postcode in most cases by using the street names depicted on the picture.
Holding a valid parcel code and a matching postcode, an unauthorized individual could access someone else’s tracking page displaying delivery information.
With the valid session token granted, one can view the underlying JSON data, including that person’s full name, email address, mobile phone number, and more.
Also Read: October 2021 PDPC Incidents and Undertaking: Lessons from the Cases
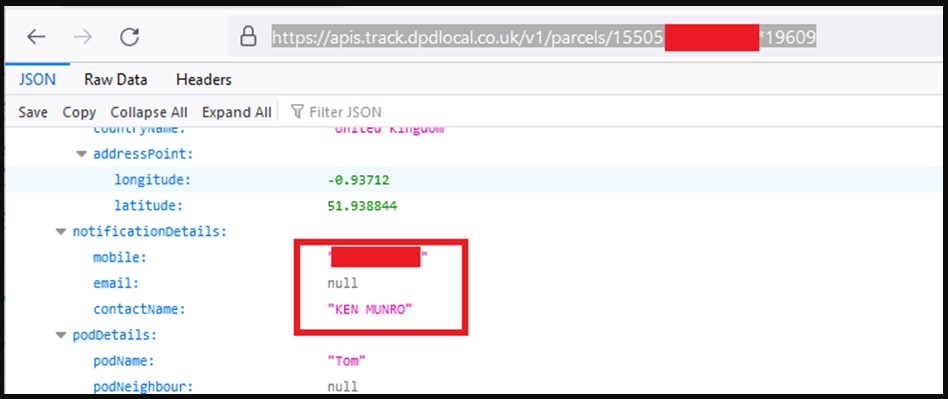
Pen Test Partners discovered the problem on September 02, 2021, and alerted DPD immediately. The firm evaluated the issue for a month and eventually pushed a fix on October 2021.
As such, the API access vulnerability remained available for exploitation for at least a month, but the window of opportunity was probably much more extensive.
Although the researchers likely were the first to discover this, the scenario of “silent” long-term abuse cannot be excluded.
The way this API attack worked is random, as one cannot guess parcel numbers for given identities, but it would still be useful in the hands of phishing actors.
Knowing the shipping status details and the matching contact details sets the stage for a successful phishing attack.
Parcel delivery service providers were the most imitated type of companies by phishing campaigns at the end of 2021, so this is already a highly-targeted sector.
We have reached out to DPD Group to request more information on the API flaw and its potential impact on customers, but we have not heard back from the firm yet.