KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Precious metal online retailer JM Bullion has disclosed a data breach after their site was hacked to include malicious scripts that stole customers’ credit card information.
JM Bullion is an online retailer of gold, silver, copper, platinum, and palladium products, including coins and bullion.
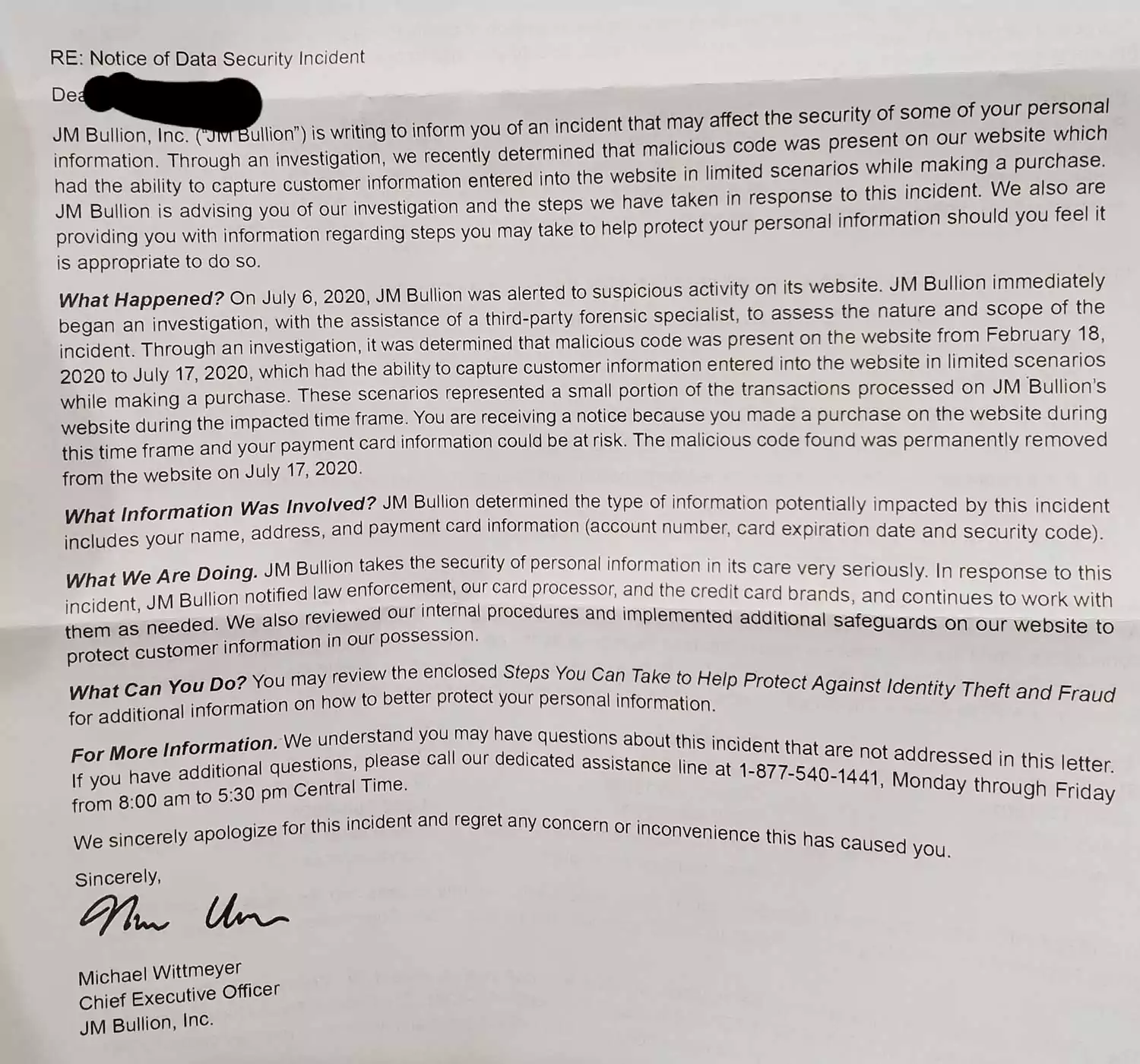
According to a ‘Notice of Data Security Incident’ sent to customers, JM Bullion’s web site was hacked in the middle of February 2020, when a malicious script was added to the site.
The malicious scripts were present on the site between February 18th, 2020, and July 17th, 2020, and caused any submitted payment information to be sent to a remote server under the attacker’s control.
Also Read: How To Prevent WhatsApp Hack: 7 Best Practices
“On July 6, 2020, JM Bullion was alerted to suspicious activity on its website. JM Bullion immediately began an investigation, with the assistance of a third-party forensic specialist, to assess the nature and scope of the incident. Through an investigation, it was determined that malicious code was present on the website from February 18, 2020 to July 17, 2020, which had the ability to capture customer information entered into the website in limited scenarios while making a purchase,” JM Bullion’s data security incident stated.
This type of compromise is known as a MageCart attack and consists of hackers compromising a website to inject malicious JavaScript scripts into various web site sections. These scripts wait for payment information to be entered by the customer, which is then stolen and sent to a remote server under the hacker’s control.
As part of this breach, attackers could steal customers’ names, addresses, and payment card information, including the account number, expiration date, and security codes.
The malicious code was removed from the site on July 17th, 2020, and JM Bullion notified law enforcement, their credit card processor, and all impacted credit card brands.
All customers who made purchases on JM Bullion’s site between February 18th, 2020, to July 17th, 2020, should monitor their credit card statements for fraudulent activity.
If any activity is discovered, it should immediately be reported to the associated credit card company as fraud.
Also Read: 15 Best Tools For Your Windows 10 Privacy Settings Setup