KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






Asian media firm E27 has been hacked, and attackers ask for a small “donation” to provide information on the vulnerabilities used in the attack.
E27 is a media company that offers Asian technology startup news and a community where members can communicate and learn from each other.
In an email notification to their members sent today and shared with BleepingComputer by Cyble, E27 CEO Mohan Belani explained that they were victims of a “malicious cyber attack”.
“We regret this has taken place and apologise for any inconvenience this may have caused you.”
“We use Facebook and LinkedIn for account login and do not store any passwords on our system. If you use the legacy email and password login, your passwords are encrypted, but we highly encourage that you change it. We do not store any credit card or payment related information on our servers.”
“The reason we are informing you is because we believe it’s the right thing to do and we want to be transparent. As a company, we believe that all community relationships must be built on trust and we want to be responsible members of the tech ecosystem. That is why we believe it is important to inform you of this incident,” E27’s notification read.
In a statement to BleepingComputer, Belani stated that they have contacted law enforcement and will be awaiting their guidance.
“We have alerted the relevant government and law enforcement authorities and will take their guidance on the next steps. Our primary focus right now is to work with our various stakeholders to get the platform fully up and running so that we can serve our users and focus on our Mission. We are thankful to be working with various community leaders in the cybersecurity space who have reached out with support and guidance and offered a lot of support.”
Also read: 9 Policies For Security Procedures Examples
This cyberattack was conducted by a hacking group identifying themselves as “Korean Hackers” and “Team Johnwick”.
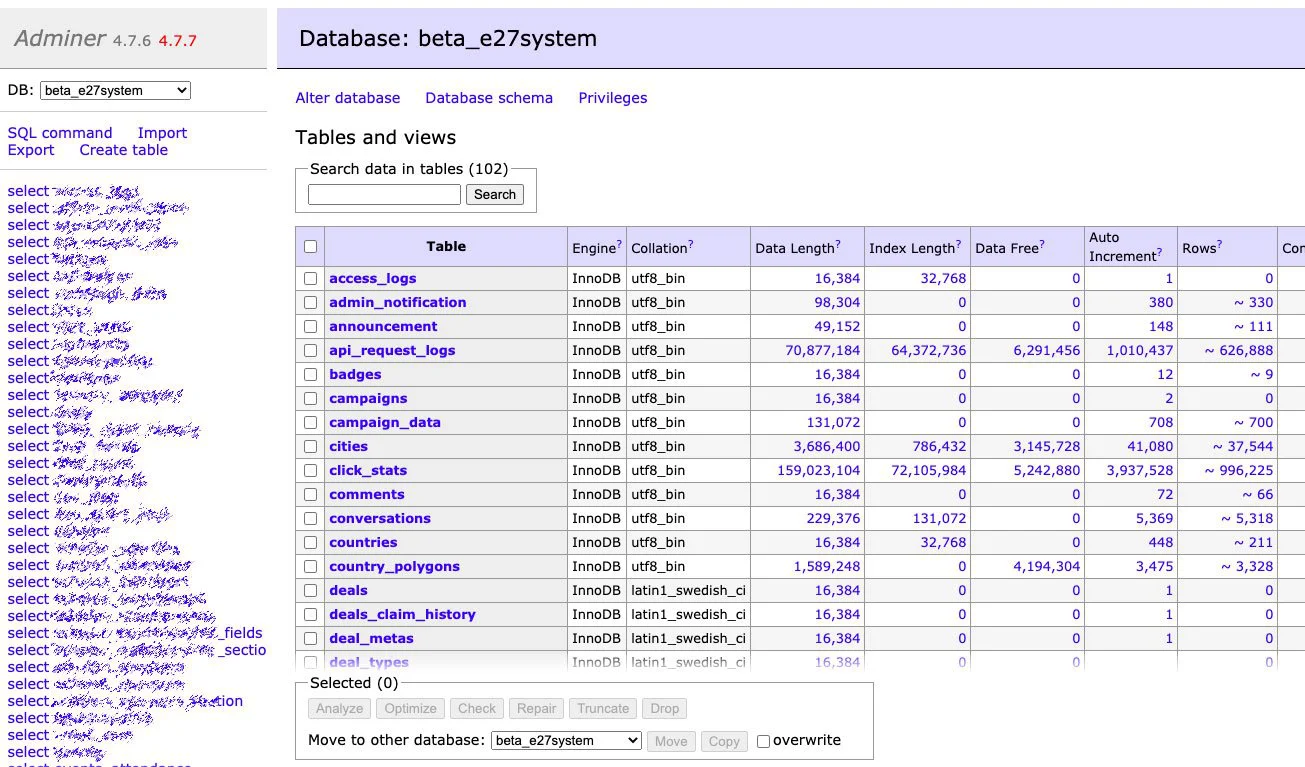
In an email sent to BleepingComputer, the hacking group claims they stole “Source code” and a “Database – contains -> (emails, mobile, passwords, others docs, profile images, etc…. ).”
As proof of this attack, they provided images of the server’s file system and databases.
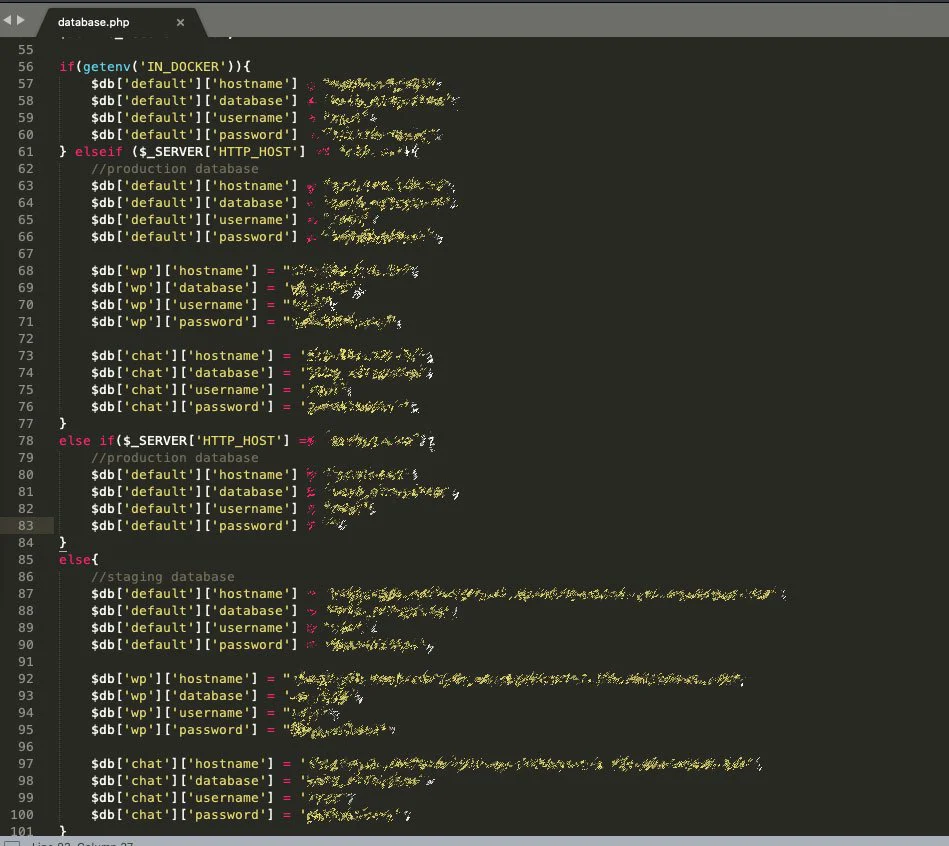
An image showing stolen was source code that contains the user name’s and passwords for the company’s databases was also sent to BleepingComputer.
Similar to this group’s recent hack of Zee5, Team Johnwick is asking E27 for a “small donation” to learn how they were hacked and help fix the vulnerabilities.
If you are a member of E27, you should immediately change your password at the site.
If you use the same password at other sites, it is strongly advised that you change it at those sites.
When changing your passwords, please use a unique password at every site that you visit.
The use of unique passwords at every site prevents data breaches at one site from affecting you at another.
Also read: 7 Client Data Protection Tips to Keep Customers Safe