KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







The Metropolitan Police Department has confirmed that they suffered a cyberattack after the Babuk ransomware gang leaked screenshots of stolen data.
The Metropolitan Police Department, also known as the DC Police or MPD, is the primary law enforcement agency for Washington, DC, the US capital.
In a statement to BleepingComputer, the DC Police stated that they are aware of a breached server and that the FBI is investigating the matter.
“We are aware of unauthorized access on our server. While we determine the full impact and continue to review activity, we have engaged the FBI to fully investigate this matter.” – Metropolitan Police Department.
This statement comes after the Babuk Locker gang said they had compromised the DC Police’s networks and stolen 250 GB of unencrypted files.
As part of this leak, the ransomware gang posted screenshots of various folders they allegedly stole during the attack. The folder names appear to contain a lot of files related to operations, disciplinary records, and files related to gang members and ‘crews’ operating in DC.
The ransomware gang warned on the data leak page that the MPD has 3 days to contact them or the threat actors will start contacting gangs to warn them of police informants.
Also Read: 4 Best Practices On How To Use SkillsFuture Credit
“Hello! Even an institution such as DC can be threatened, we have downloaded a sufficient amount of information from your internal networks, and we advise you to contact us as soon as possible, to prevent leakage, if no response is received within 3 days, we will start to contact gangs in order to drain the informants, we will continue to attack the state sector of the usa, fbi csa, we find 0 day before you, even larger attacks await you soon,” stated the Babuk ransomware gang on their data leak site.
One of the screenshots includes the 4/19/2021 timestamp for all the folders, which is likely when the threat actors stole the data.
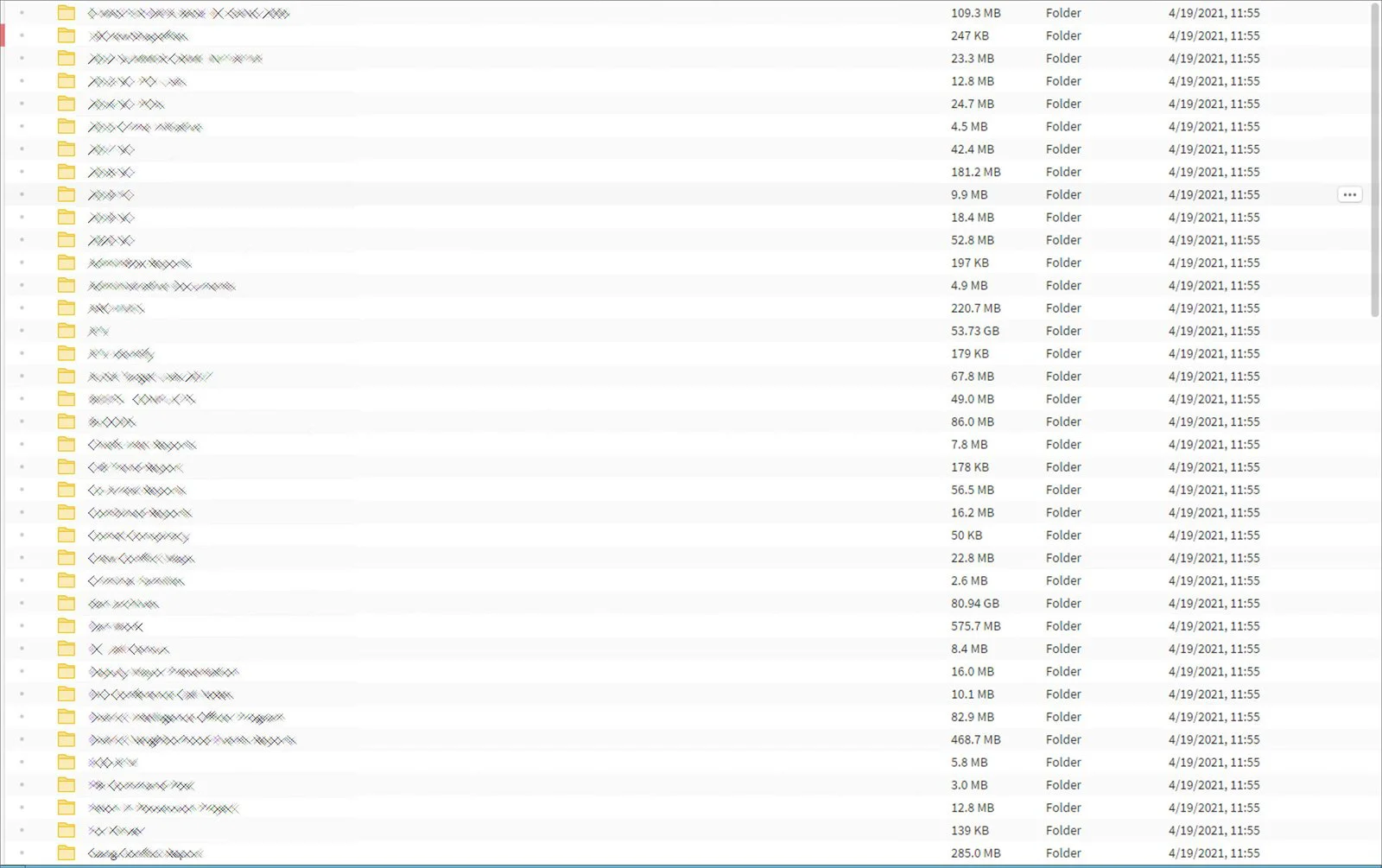
The Babuk gang specifically pointed out one of the files, which based on the title, is related to arrests after the January 6th protest that stormed the Capital Building.
We were the first to report on the Babuk Locker ransomware in January when they began operating and leaking victim’s data on hacker forums.
Since then, they have slowly increased their activity as they recruit further hackers to work with them and compromise more enterprise networks.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
They recently made the news when cybersecurity firm Emsisoft discovered that their decryptor contained severe bugs that could destroy files while they were being decrypted.
Update 4/26/21 9:42 PM EST: Added updated statement from the Babuk ransomware gang.