KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Planned Parenthood Los Angeles has disclosed a data breach after suffering a ransomware attack in October that exposed the personal information of approximately 400,000 patients.
According to a data breach notification sent to Planned Parenthood Los Angeles (‘PPLA’) patients, the cyberattack occurred between October 9th and 17th, allowing threat actors to steal files from the compromised network.
“On October 17, 2021, we identified suspicious activity on our computer network. We immediately took our systems offline, notified law enforcement, and a third-party cybersecurity firm was engaged to assist in our investigation,” explained the notification sent to affected patients.
“The investigation determined that an unauthorized person gained access to our network between October 9, 2021 and October 17, 2021, and exfiltrated some files from our systems during that time.”
However, it wasn’t until November 4th that PPLA determined that the stolen files contained patients’ personal information, including their “address, insurance information, date of birth, and clinical information, such as diagnosis, procedure, and/or prescription information.”
Also Read: How a Smart Contract Audit Works and Why it is Important
In a statement to the Washington Post, who first reported on the breach, PPLA spokesperson John Erickson said the stolen files contained the personal data of approximately 400,000 patients and was caused by a ransomware attack.
When threat actors conduct ransomware attacks, they lurk in a compromised network for days, if not weeks, while quietly stealing files and uploading them to their servers.
Once they have finished harvesting valuable data, the threat actors deploy ransomware to encrypt all the devices on the network.
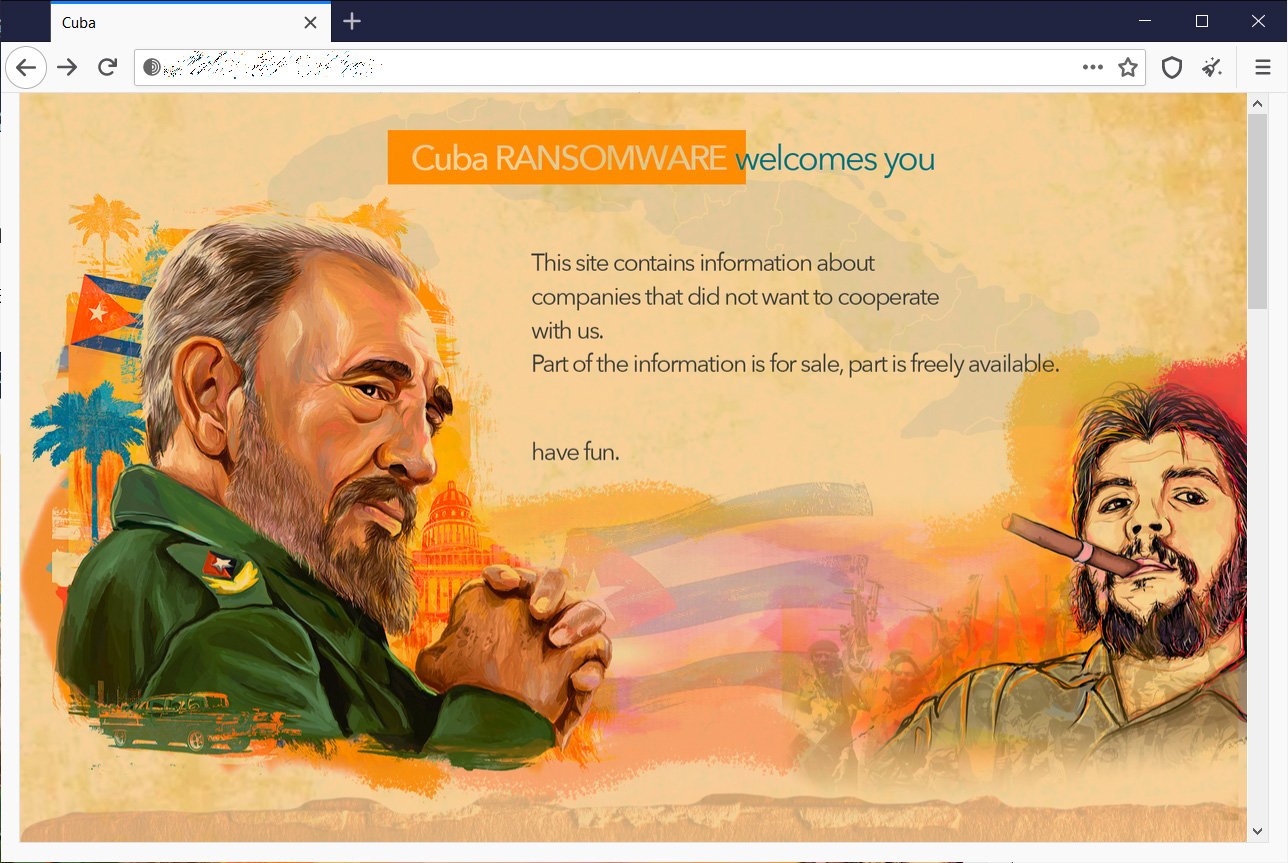
They then use the stolen data as leverage to scare victims into paying a ransom, or the data will be publicly released on a ransomware gang’s data leak site.
It is unknown what ransomware gang is responsible for the attack and whether a ransom has been paid.
However, if a ransom is not paid, we will likely learn who is responsible after the data is published.
As the stolen data is said to contain medical information, including the procedures undertaken at PPLA, the public release of the data could significantly impact affected patients.
Also Read: How To Secure Your WiFi Camera: 4 Points To Consider
While no financial information was exposed by the breach, names, addresses, date of birth, and health information was accessed that could allow threat actors to perform more targeted attacks.
Due to this, all affected patients should be on the lookout for strange emails or SMS texts regarding their PPLA visits, health information, or other related information.
If patients receive any emails claiming to be from PPLA and asking for sensitive information, they should immediately contact Planned Parenthood to see if the emails are legitimate.