KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







T-Mobile has confirmed that threat actors hacked their servers in a recent cyber attack but still investigate whether customer data was stolen.
Yesterday, news broke that a threat actor was selling the alleged personal data for 100 million T-Mobile customers after they breached database servers operated by the mobile network.
The hacker told BleepingComputer that the databases stolen during the attack contain the data for approximately 100 million T-Mobile customers, including IMSI numbers, IMEI numbers, phone numbers, customer names, security PINs, Social security numbers, driver’s license numbers, and date of birth.
This data was stolen approximately two weeks ago and contains customer data going back as far as 2004.
“Their entire IMEI history database going back to 2004 was stolen,” the hacker told BleepingComputer.
When we contacted T-Mobile yesterday, they stated that they were aware of the claims and were actively investigating whether they were breached.
Also Read: 4 Reasons Why You Need an Actively Scanning Antivirus Software
In an email sent to BleepingComputer, T-Mobile has confirmed that some of their servers were hacked in the reported attack and are continuing to investigate if customer data was accessed.
“We have been working around the clock to investigate claims being made that T-Mobile data may have been illegally accessed. We take the protection of our customers very seriously and we are conducting an extensive analysis alongside digital forensic experts to understand the validity of these claims, and we are coordinating with law enforcement.
We have determined that unauthorized access to some T-Mobile data occurred, however we have not yet determined that there is any personal customer data involved. We are confident that the entry point used to gain access has been closed, and we are continuing our deep technical review of the situation across our systems to identify the nature of any data that was illegally accessed. This investigation will take some time but we are working with the highest degree of urgency. Until we have completed this assessment we cannot confirm the reported number of records affected or the validity of statements made by others.
We understand that customers will have questions and concerns, and resolving those is critically important to us. Once we have a more complete and verified understanding of what occurred, we will proactively communicate with our customers and other stakeholders.” – T-Mobile.
While T-Mobile is continuing its investigation, screenshots of the stolen databases and servers accessed by the attackers indicate that the threat actors downloaded customer data during the cyberattack.
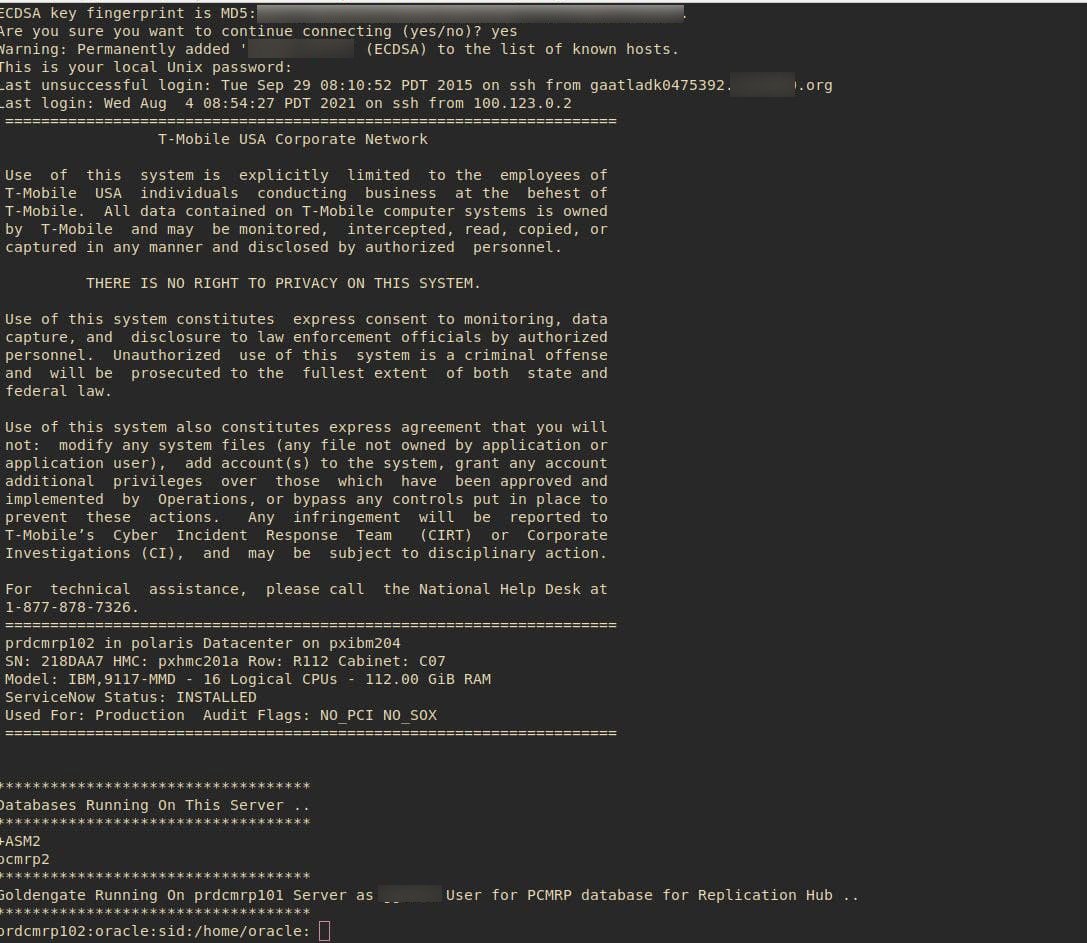
One screenshot shared with BleepingComputer shows the threat actors connecting to an Oracle database server over SSH on the company’s internal data center network.
If it is revealed that customer data was stolen during the attack, which is expected, this will be a significant breach as threat actors will have enough information to attempt SIM swapping attacks.
Using these attacks, the attackers can transfer a phone number to their own devices to receive password reset and multi-factor authentication requests that could allow them to breach other accounts belonging to a customer.
This would be the sixth data breach suffered by T-Mobile in the past four years:
As the attackers told BleepingComputer they have offers from other threat actors to purchase the data, T-Mobile customers should operate under the assumption that their data was exposed.
Also Read: 5 Types of Ransomware, Distinguished
All T-Mobile customers should be on the lookout for suspicious emails or SMS texts pretending to be from T-Mobile.
If any are received, do not click any links embedded in the messages as threat actors could use them to harvest credentials from unsuspecting T-Mobile customers.