KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Google’s Threat Analysis Group (TAG) says that North Korean government-sponsored hackers are once again targeting security researchers using fake Twitter and LinkedIn social media accounts.
The hackers also created a website for a fake company named SecuriElite (located in Turkey) and supposedly offering offensive security services as the Google security team focused on hunting down state-backed hackers discovered on March 17.
All LinkedIn and Twitter accounts created by the North Korean hackers and associated with this new campaign were reported by Google and are now disabled.
Just as in the attacks detected during January 2021, this site was also hosting the attackers’ PGP public key, which was used as bait to infect security researchers with malware after triggering a browser exploit on opening the page.
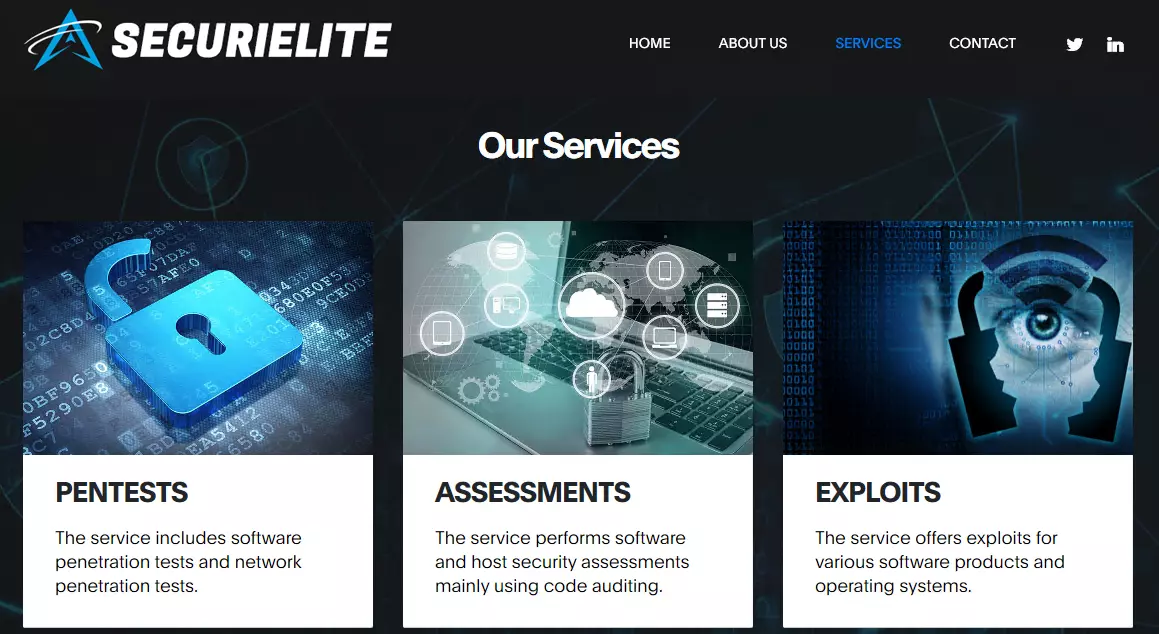
However, the attacks were spotted in their early phase since the SecuriElite site wasn’t yet set up to deliver any malicious payloads.
Also Read: 4 Best Practices On How To Use SkillsFuture Credit
“At this time, we have not observed the new attacker website serve malicious content, but we have added it to Google Safebrowsing as a precaution,” Threat Analysis Group’s Adam Weidemann said.
“Based on their activity, we continue to believe that these actors are dangerous, and likely have more 0-days.
“We encourage anyone who discovers a Chrome vulnerability to report that activity through the Chrome Vulnerabilities Rewards Program submission process.”
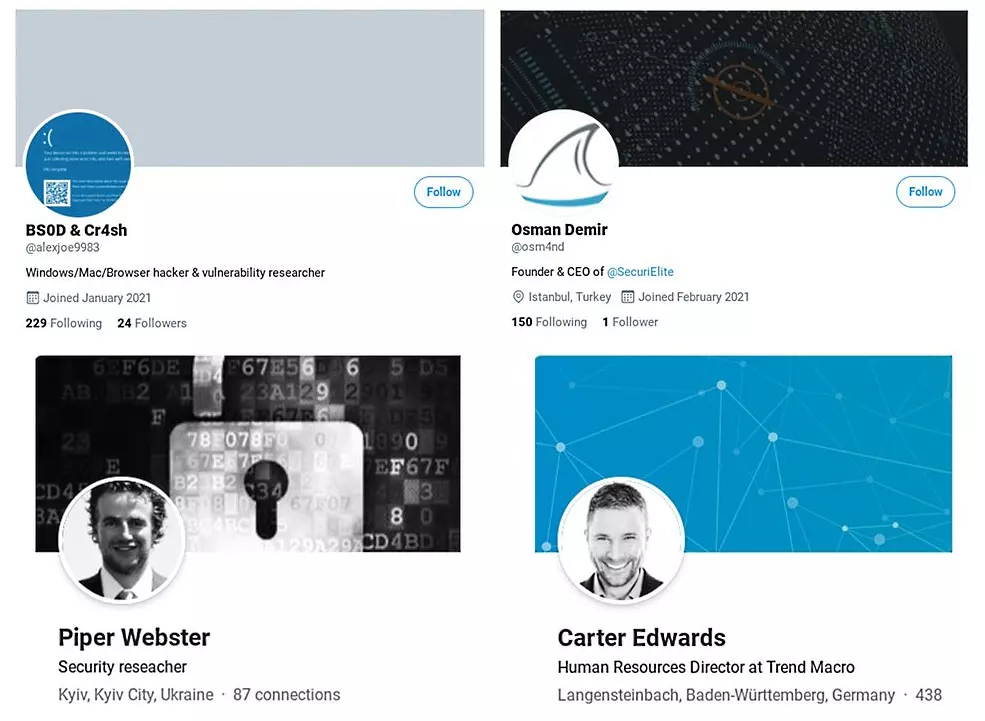
In January, North Korean state hackers tracked as the Lazarus Group targeted security researchers in social engineering attacks using elaborate fake “security researcher” social media personas.
The attackers sent malicious Visual Studio Projects and links to a malicious website hosting exploit kits designed to install backdoors on targeted researchers’ computers.
Some researchers using fully patched Windows 10 computers and running the latest Google Chrome version were infected in the attacks, indicating that the hackers were using zero-day vulnerabilities to compromise the targets’ devices.
An additional Internet Explorer zero-day was discovered by South Korean cybersecurity firm ENKI after failed attacks on their security researchers.
Also Read: 3 Reasons Why You Must Take A PDPA Singapore Course
Microsoft also reported that they had also been tracking the attack and saw Lazarus operators sending MHTML files with malicious JavaScript to researchers.

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
