KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





The European Medicines Agency (EMA) today revealed that some of the Pfizer/BioNTech COVID-19 vaccine data stolen from its servers in December was leaked online.
EMA is a decentralized agency responsible for reviewing and approving COVID-19 vaccines, as well as for evaluating, monitoring, and supervising any new medicines introduced to the EU.
“The ongoing investigation of the cyberattack on EMA revealed that some of the unlawfully accessed documents related to COVID-19 medicines and vaccines belonging to third parties have been leaked on the internet,” EMA said today. “Necessary action is being taken by the law enforcement authorities.”
“The Agency continues to fully support the criminal investigation into the data breach and to notify any additional entities and individuals whose documents and personal data may have been subject to unauthorized access.”
Also Read: How Formidable is Singapore Cybersecurity Masterplan 2020?
EMA also said that European medicines regulatory network is fully functional and COVID-19 evaluation and approval timelines are not affected by the incident.
On December 31st, BleepingComputer became aware of threat actors leaking what they claimed was the stolen EMA data on several hacker forums. Below is a screenshot of one of the leaks seen by BleepingComputer at the time.
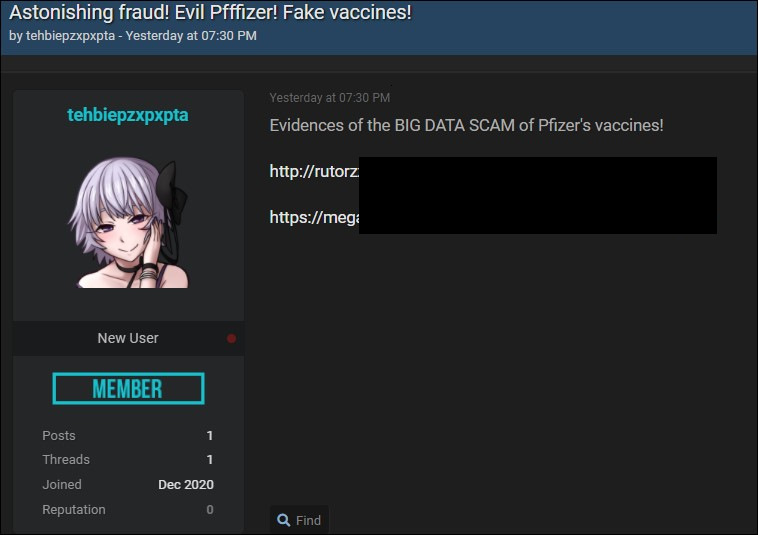
Sources in the cybersecurity intelligence community have told BleepingComputer that the leaked stolen data includes email screenshots, EMA peer review comments, Word documents, PDFs, and PowerPoint presentations.
The agency disclosed in December that it launched a joint investigation of the attack in cooperation with law enforcement and other relevant entities.
On the same day, Pfizer and BioNTech jointly disclosed that some of the COVID-19 documents submitted to EMA were accessed by the threat actors behind the cyberattack.
“Today, we were informed by the European Medicines Agency (EMA) that the agency has been subject to a cyberattack and that some documents relating to the regulatory submission for Pfizer and BioNTech’s COVID-19 vaccine candidate, BNT162b2, which has been stored on an EMA server, had been unlawfully accessed,” Pfizer’s and BioNTech’s joint statement said.
In subsequent updates, EMA said that the investigation revealed that only a limited number of documents were accessed without authorization.
Also Read: Going Beyond DPO Meaning: Ever Heard of Outsourced DPO?
EMA also found that the data breach was limited to a single IT application with the attackers primarily targeting data related to COVID-19 medicines and vaccines.
Multiple threat actors including state-sponsored hacking groups [1, 2, 3] have targeted organizations involved in COVID-19 vaccine research and delivery after the start of the pandemic.