KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






The Microsoft Defender Advanced Threat Protection (ATP) endpoint security platform now provides users with a new report designed to help them keep track of vulnerable Windows and macOS devices within their organization’s environment.
The vulnerable devices report displays graphs with statistics and details on currently vulnerable device trends with the end goal of making it easier for IT administrators to grasp the scope and breadth of device exposure within the organization.
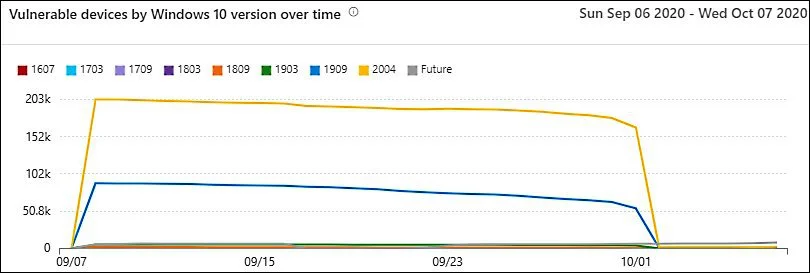
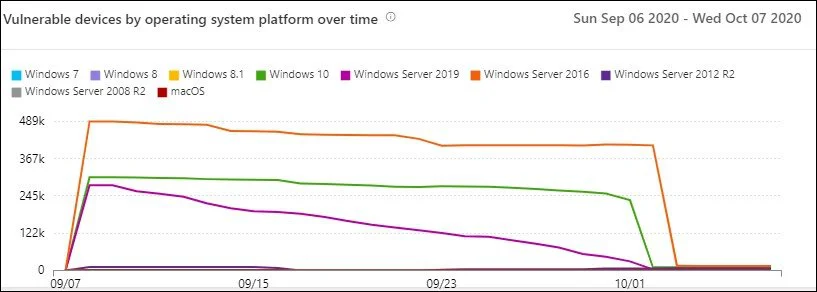
“You can filter the data by vulnerability severity levels, exploit availability, vulnerability age, operating system platform, Windows 10 version, or device group,” Microsoft explains.
Also Read: Thinking of Shredding or Burning Paper? Here’s What You Should Know
“If there is an insight you want to explore further, select the relevant bar chart to view a filtered list of devices in the Device inventory page. From there, you can export the list.”
Among the insights administrators can draw from this new Microsoft Defender ATP report (recently renamed to Microsoft Defender for Endpoint), Microsoft highlights:
For instance, the severity level graph will show the number of devices based on the most severe vulnerability detected for each of them, while the exploit availability graph will display the number of vulnerable devices based on the highest level of known exploit.
Admins can also access vulnerability age graphs, get the number of vulnerable devices by operating system platform graphs, as well as the number of vulnerable devices by Windows 10 version.
The report is in public preview starting today and admins can access it by going to Reports > Vulnerable devices in the Microsoft Defender Security Center after toggling on preview features.
Starting with July, Microsoft Defender ATP also added the Microsoft Secure Score for Devices feature that can evaluate the collective security configuration state of devices on an enterprise network.
Also Read: What Legislation Exists in Singapore Regarding Data Protection and Security?
The feature identifies unprotected systems and provides recommended actions to increase the security of an organization’s endpoints.
A detailed description of the procedure that needs to be followed to address the issues found by Microsoft Secure Score for Devices while assessing their network devices is available here.