KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Microsoft has announced a new feature for Microsoft Defender for Endpoint (MDE) to help organizations prevent attackers and malware from using compromised unmanaged devices to move laterally through the network.
This new feature allows admins to “contain” unmanaged Windows devices on their network if they were compromised or are suspected to be compromised.
Once tagged as contained, the enterprise endpoint security platform will instruct Windows systems on the network to block all communication to and from the device.
Also Read: The Top 4W’s of Ethical Hacking
This can help stop malicious actors from moving laterally within the organization using unmanaged devices and prevent spreading an infection that would otherwise cause further damage.
“This action can help prevent neighboring devices from becoming compromised while the security operations analyst locates, identifies, and remediates the threat on the compromised device,” Microsoft explains.
However, there’s a catch: the new MDE capability works only with onboarded devices running Windows 10 and later or Windows Server 2019 and later.
“Only devices running on Windows 10 and above will perform the Contain action meaning that only devices running Windows 10 and above that are enrolled in Microsoft Defender for Endpoint will block ‘contained’ devices at this time,” Microsoft added.
This means that, although contained from all managed Windows devices on the network, the contained system will still be able to access other devices that haven’t been onboarded.
Also Read: What is Social Engineering and How Does it Work?
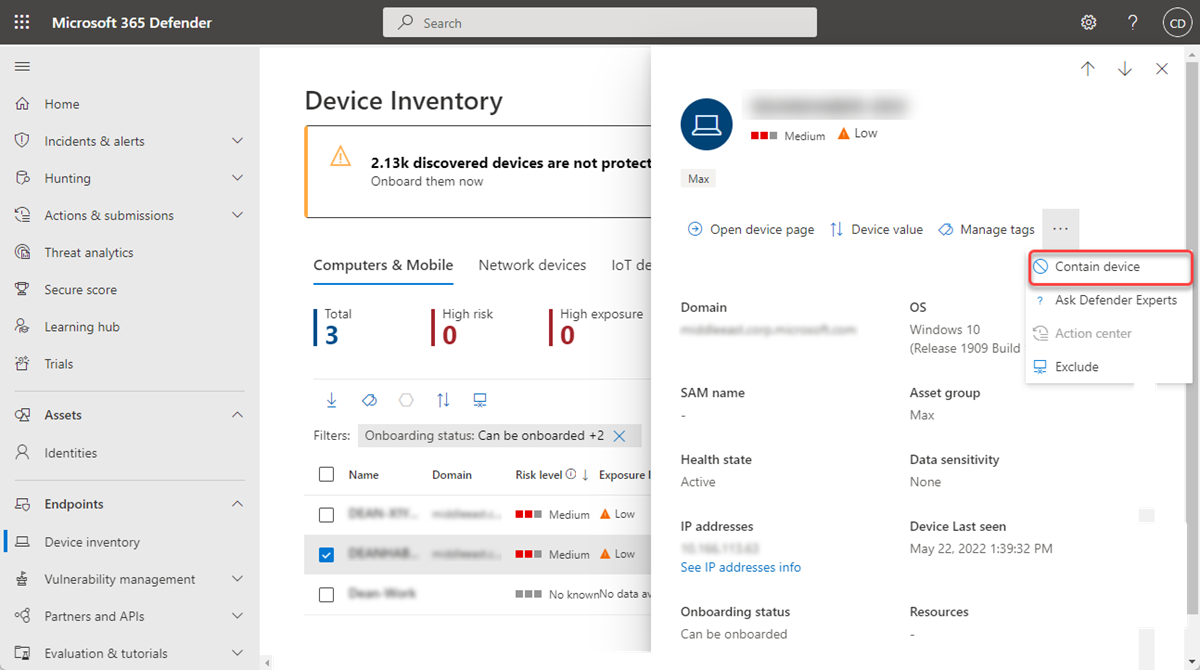
To contain a device that is potentially compromised, admins have to go through the following steps:
After you contain an unmanaged device, it can take up to 5 minutes for Microsoft Defender for Endpoint onboarded devices to start blocking communications.
If any of the contained devices on the network will change its IP address, all enrolled devices will recognize this and begin blocking communications with the new IP address.
To stop containing a specific device, select it from ‘Device inventory’ or open the device page. Then you need to select ‘Release from containment’ from the action menu to restore the device’s connection to the network.