KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







Microsoft has announced that Excel 4.0 (XLM) macros will now be disabled by default to protect customers from malicious documents.
In October, the company first revealed in a Microsoft 365 message center update that it would disable XLM macros in all tenants if the users or admins hadn’t manually toggled the feature on or off.
Starting July 2021, Windows admins could also use group policies and users the ‘Enable XLM macros when VBA macros are enabled’ setting from the Excel Trust Center to disable this feature manually.
Also Read: Data Protection Policy: 8 GDPR Compliance Tips
“In July of 2021, we released a new Excel Trust Center setting option to restrict the usage of Excel 4.0 (XLM) macros,” said Catherine Pidgeon, a Principal Program Manager Lead at Microsoft, earlier this week in a Tech Community blog post.
“As planned, we have now made this setting the default when opening Excel 4.0 (XLM) macros. This will help our customers protect themselves against related security threats.”
Admins can configure how Excel macros are allowed to run using Group Policy settings, Cloud policies, and ADMX policies.
They can also block all Excel XLM macro use in their environments (including new user-created files) by toggling on the “Prevent Excel from running XLM macros” Group Policy, configurable via Group Policy Editor or registry key.
Right now, XLM macros are disabled by default in the September fork, Excel version 16.0.14527.20000 and newer available in the:
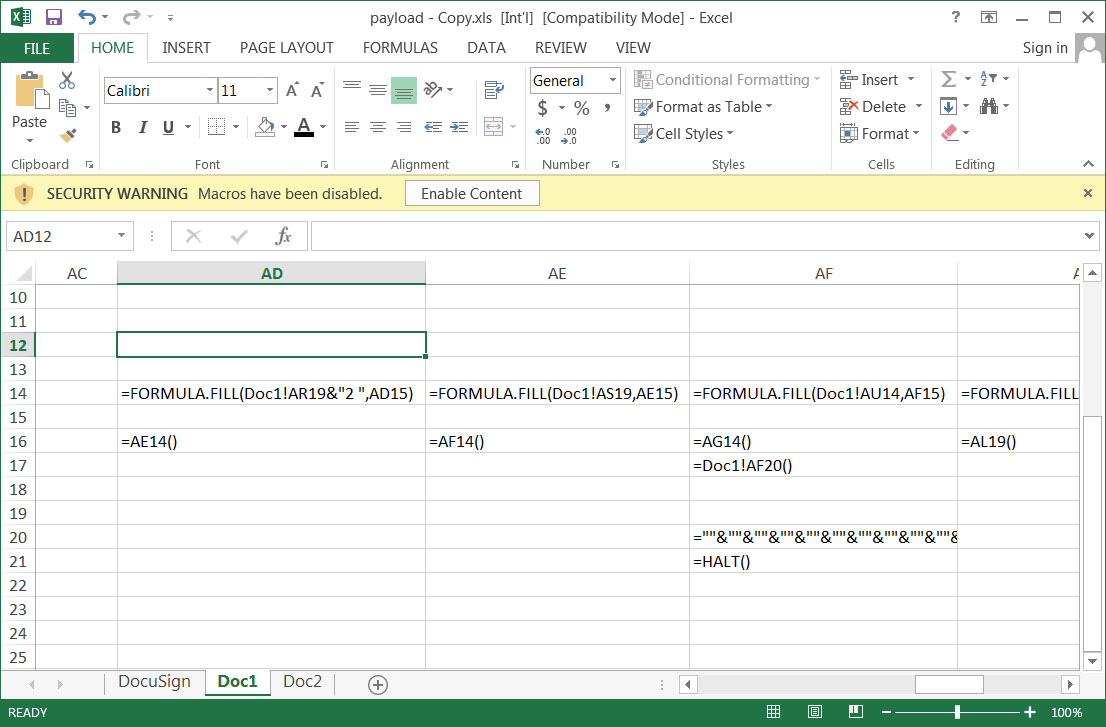
Even though VBA-based macros were introduced with the release of Excel 5.0, threat actors are still using them more than two decades later to create documents that deploy malware or perform other malicious behavior.
Also Read: Don’t Be Baited! 5 Signs of Phishing in Email
Malicious campaigns using XLM macros to push malware have been observed downloading and installing TrickBot, Zloader, Qbot, Dridex, and many other strains on victims’ computers.
Microsoft also silently added a Group Policy in October 2019 that allows admins to block Excel users from opening untrusted (and potentially malicious) Microsoft Query files with IQY, OQY, DQY, and RQY extensions.
Such files have been weaponized in numerous malicious attacks to deliver remote access Trojans and malware loaders since early 2018.