KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A new threat actor is hacking Microsoft Exchange servers and breaching corporate networks using the ProxyShell vulnerability to deploy the Babuk Ransomware.
The ProxyShell attacks against vulnerable Microsoft Exchange servers started several months ago, with LockFile and Conti being among the first ransomware groups to exploit them.
The name Tortilla is based on malicious executables spotted in campaigns using the name Tortilla.exe.
Also Read: How To Comply With PDPA: A Checklist For Businesses
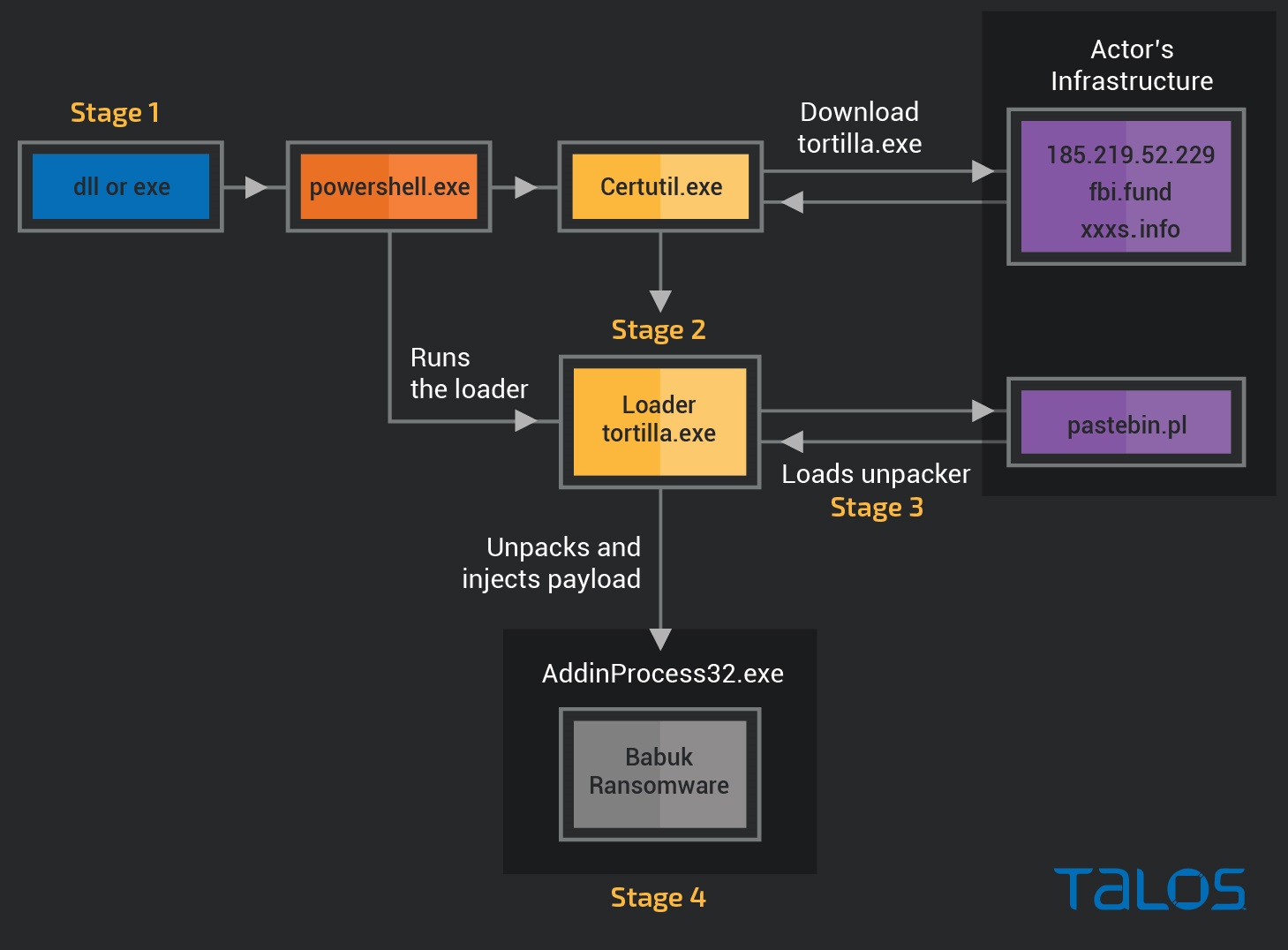
The Babuk ransomware attack starts with a DLL, or .NET executable dropped on the Exchange server using the ProxyShell vulnerability.
The Exchange IIS worker process w3wp.exe then executes this malicious payload to execute obfuscated PowerShell command that features endpoint protection bypassing, eventually invoking a web request to fetch a payload loader named ‘tortilla.exe.’
This loader will connect to ‘pastebin.pl’ and download a payload that is loaded into memory and injected into a NET Framework process, which ultimately encrypts the device with the Babuk Ransomware.
Although Cisco analysts found evidence of ProxyShell vulnerability exploitation in most infections, most notably the ‘China Chopper’ web shell, the telemetry data reflects a broad spectrum of attempted exploits.
Also Read: In Case You Didn’t Know, ISO 27001 Requires Penetration Testing
More specifically, Tortilla followed these pathways to drop the DLL and .NET modules:
As these attacks rely on patched vulnerabilities, it is strongly advised that all admins upgrade their servers to the latest versions to prevent them from being exploited in attacks.
Babuk Locker is a ransomware operation launched at the beginning of 2021 when it began targeting businesses and encrypting their data in double-extortion attacks.
After conducting an attack on the Washinton DC’s Metropolitan Police Department (MPD), and feeling the heat from U.S. law enforcement, the ransomware gang shut down their operation.
After the source code for the first version of Babuk and a builder were leaked on hacking forums, other threat actors began utilizing the ransomware to launch their own attacks.
It is unclear if Tortilla was an affiliate of Babuk back when the RaaS was active or if they just grabbed the strain’s source code when it came out to conduct new attacks.
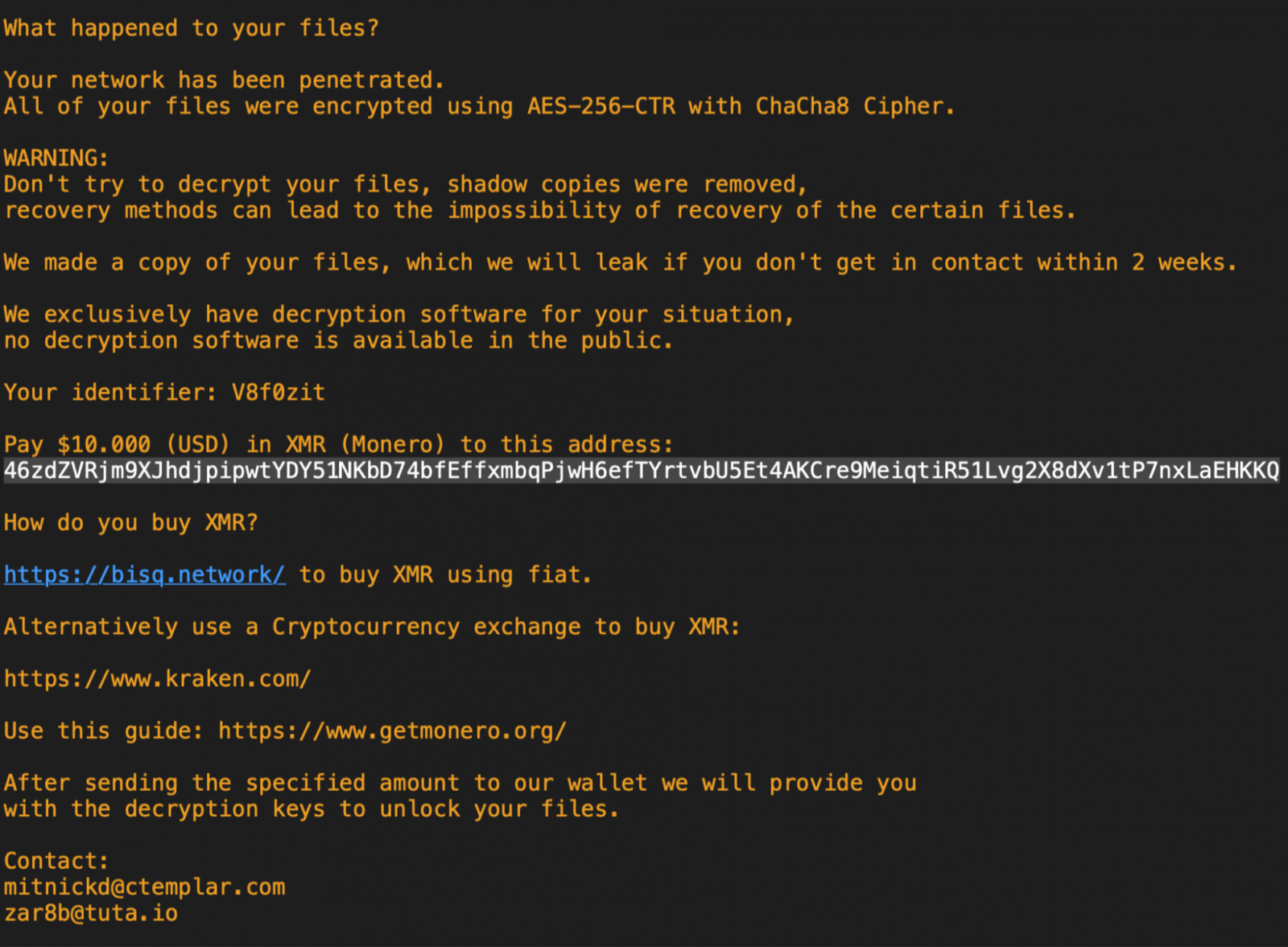
However, as the ransom note used in these attacks ask for a low $10,000 in Monero, it is likely not conducted by the original Babuk operation, who demanded far larger ransomware in Bitcoin.
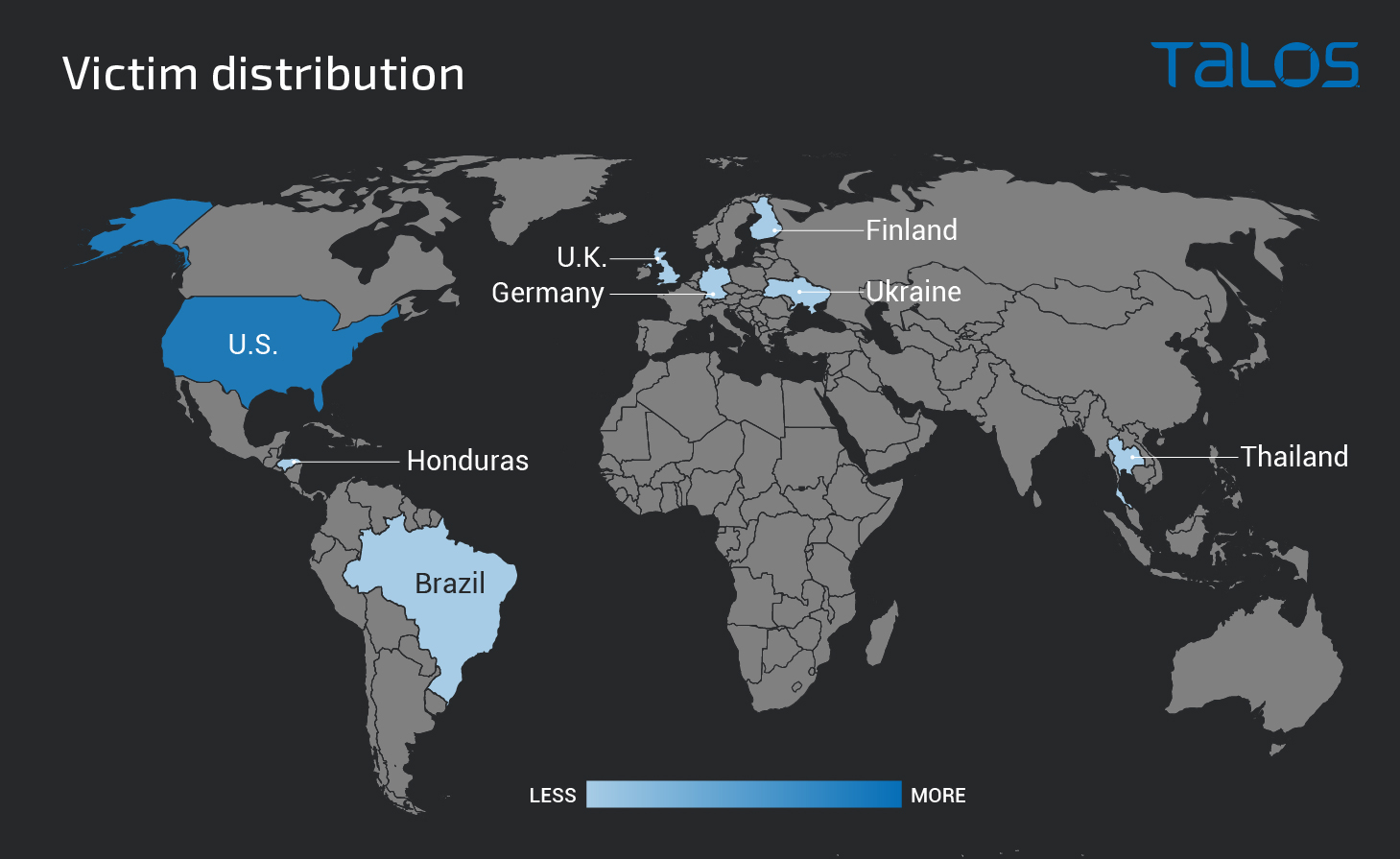
Although Talos researchers noticed some attacks in Germany, Thailand, Brazil, and the U.K., most of Tortilla’s targets are U.S.-based.
The I.P. address of the download server is located in Moscow, Russia, which could indicate the origin of these attacks, but there are no attribution conclusions in the report.
Also, the ‘pastebin.pl’ domain used for the unpacking stage has been previously abused by AgentTesla and FormBook distribution campaigns.
While a decryptor was previously released for Babuk ransomware, it can only decrypt victims whose private keys were part of the source code leak.
Therefore, threat actors can continue to use the Babuk ransomware strain to launch their own operations, such as what we are seeing with the Tortilla threat actor.