KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Microsoft has silently issued a partial fix for a local privilege escalation (LPE) vulnerability impacting all Windows 7 and Server 2008 R2 devices.
This LPE vulnerability (not yet officially tracked using a CVE ID) stems from the misconfiguration of two service registry keys and it allows local attackers to escalate privileges on any fully patched systems.
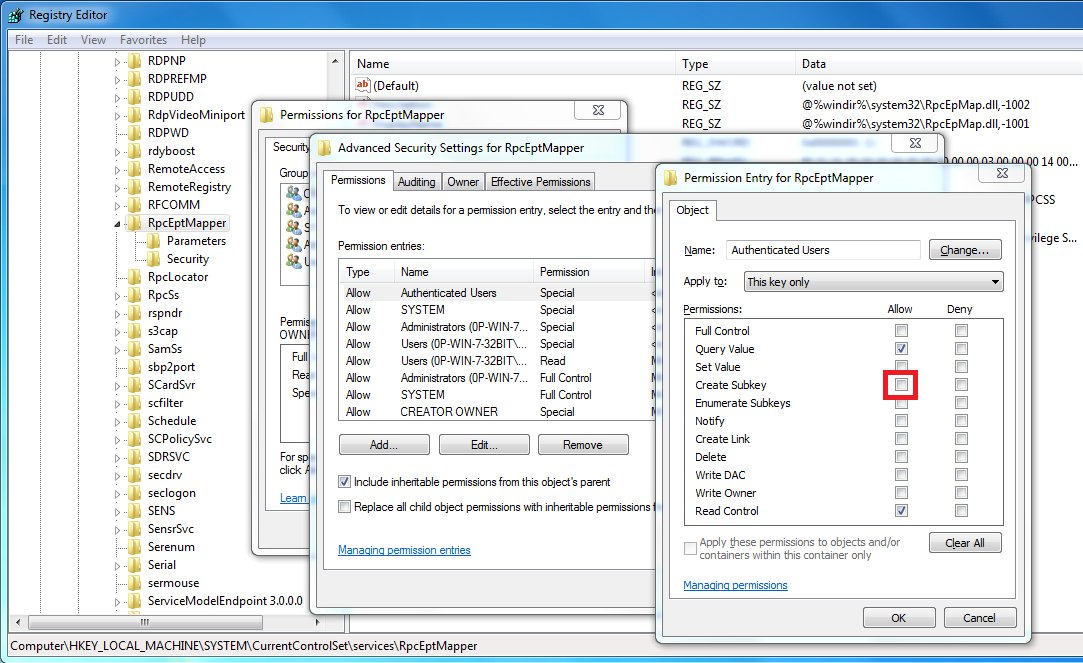
Security researcher Clément Labro discovered that insecure permissions on the registry keys of the RpcEptMapper and DnsCache services enable attackers to trick the RPC Endpoint Mapper service to load malicious DLLs on Windows 7 and Windows Server 2008R2.
By exploiting this issue, attackers can execute arbitrary code in the context of the Windows Management Instrumentation (WMI) service that runs with LOCAL SYSTEM permissions.
“In short, a local non-admin user on the computer just creates a Performance subkey in one of the above keys, populates it with some values, and triggers performance monitoring, which leads to a Local System WmiPrvSE.exe process loading attacker’s DLL and executing code from it,” 0patch co-founder Mitja Kolsek explained in November when the bug was first disclosed as a zero-day.
While Microsoft has silently addressed the issue for the RpcEptMapper registry key (as discovered by 0patch) in the April 2021 Windows Updates (ESU) release by changing permissions to no longer include ‘Create Subkey’ for groups Authenticated Users and Users, the company hasn’t yet fixed the vulnerability for DnsCache.
Also Read: The Difference Between GDPR And PDPA Under 10 Key Issues
An open-source exploit tool for this Windows 7 / 2008R2 RpcEptMapper registry key vulnerability is available since February.
This bug still affects Windows 7 and Server 2008 R2 devices, even if they are enrolled in Microsoft’s Extended Security Updates (ESU) program or not until Microsoft will release security updates for ESU customers to address the issue fully.
0patch released a temporary fix in the form of a free micropatch that fully mitigates the issue by sabotaging “performance monitoring operations for the two affected services, Dnsclient and RpcEptMapper.”
The micropatch will remain free for everyone until Microsoft fully patches the vulnerability according to 0patch.
Also Read: PDPA Compliance Singapore: 10 Areas To Work On
However, “at this point, if you are still using Windows 7 / Server 2008 R2 without isolating these machines properly in the network first, then preventing an attacker from getting SYSTEM privileges is probably the least of your worries,” as Labro said.