KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





Microsoft has released an open-source cyberattack simulator that allows security researchers and data scientists to create simulated network environments and see how they fare against AI-controlled cyber agents.
This simulator is being released as an open-source project named ‘CyberBattleSim‘ built using a Python-based Open AI Gym interface.
The Microsoft 365 Defender Research team created CyberBattleSim to model how a threat actor spreads laterally through a network after its initial compromise.
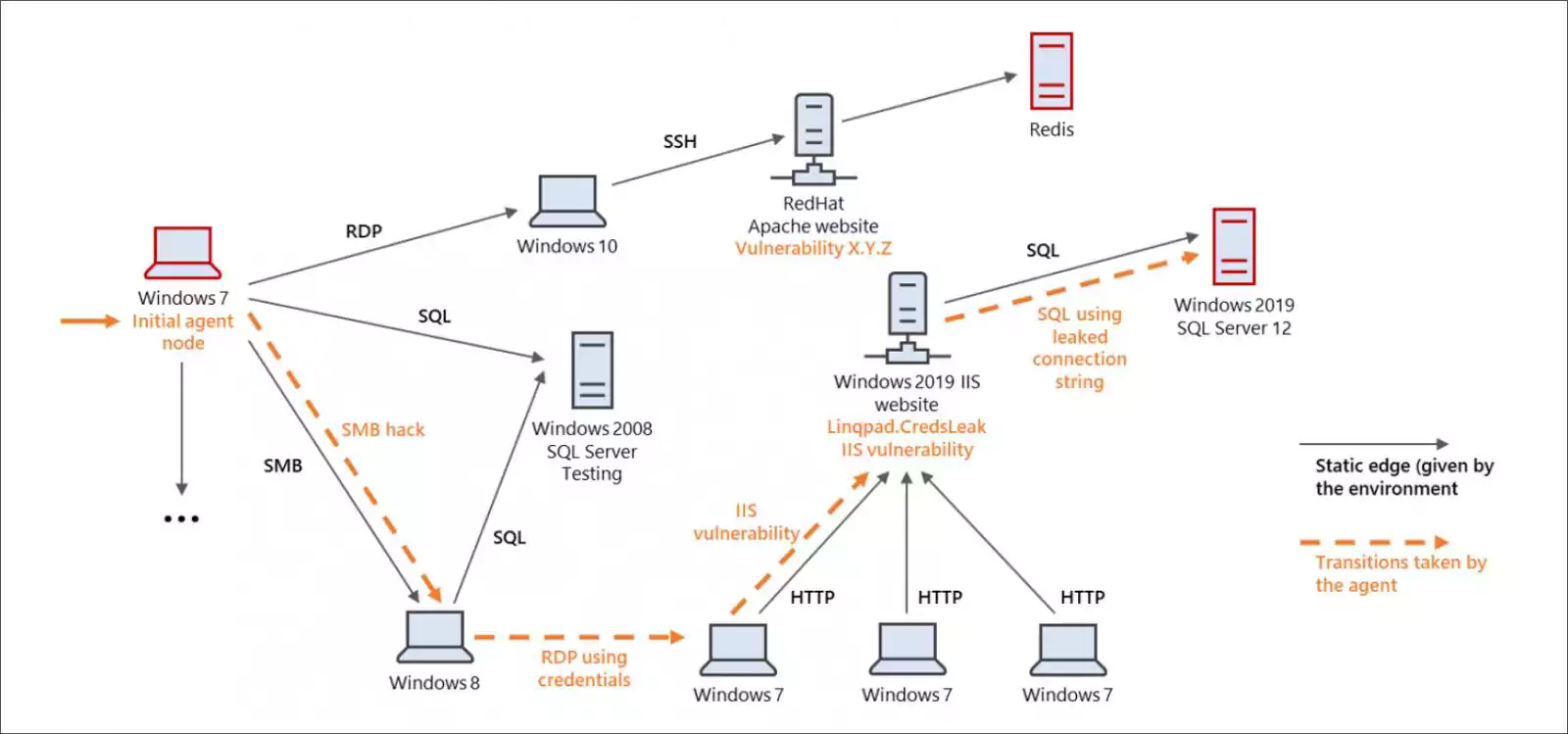
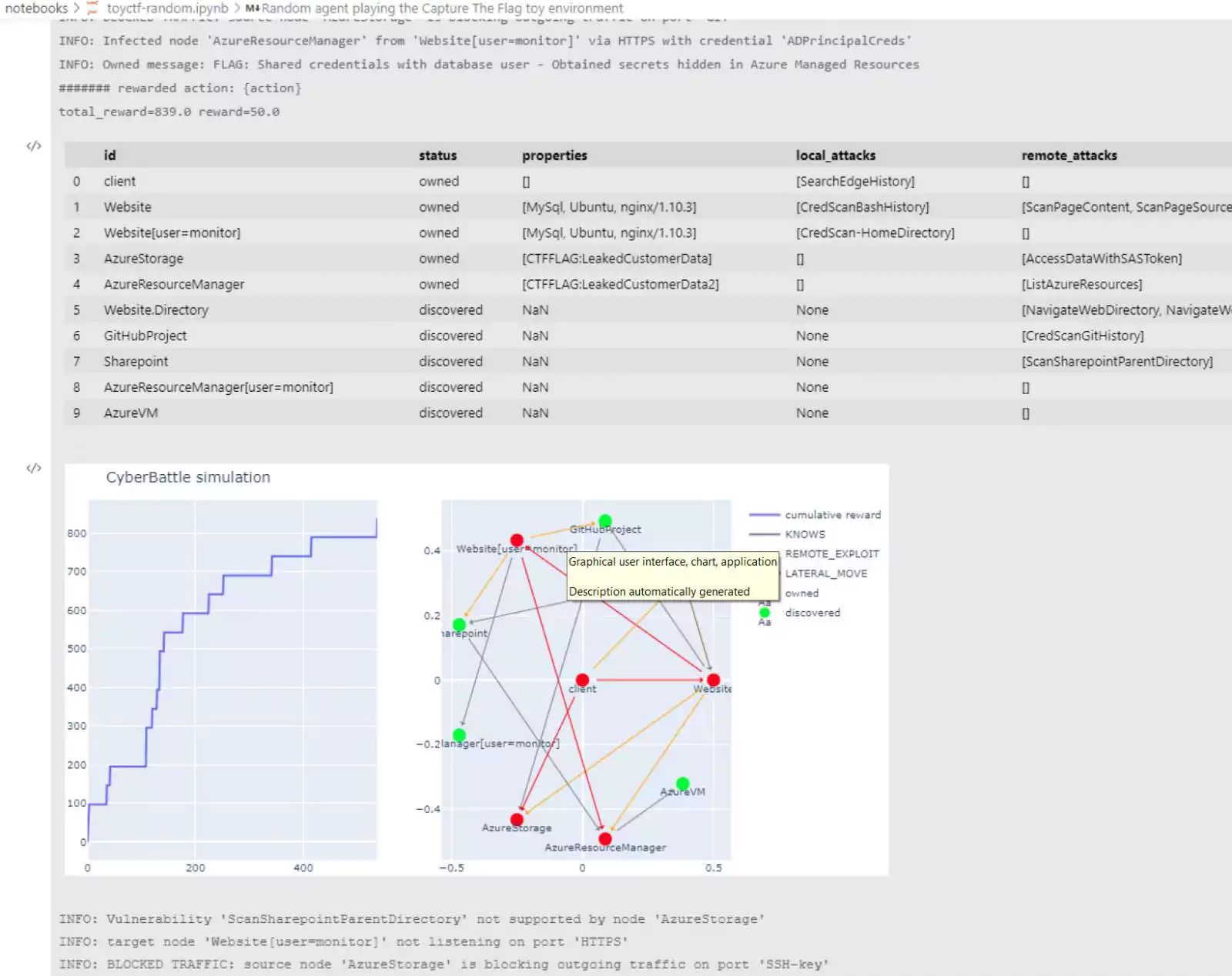
“The environment consists of a network of computer nodes. It is parameterized by a fixed network topology and a set of predefined vulnerabilities that an agent can exploit to laterally move through the network.”
“The simulated attacker’s goal is to take ownership of some portion of the network by exploiting these planted vulnerabilities. While the simulated attacker moves through the network, a defender agent watches the network activity to detect the presence of the attacker and contain the attack,” the Microsoft 365 Defender Research Team explains in a new blog post.
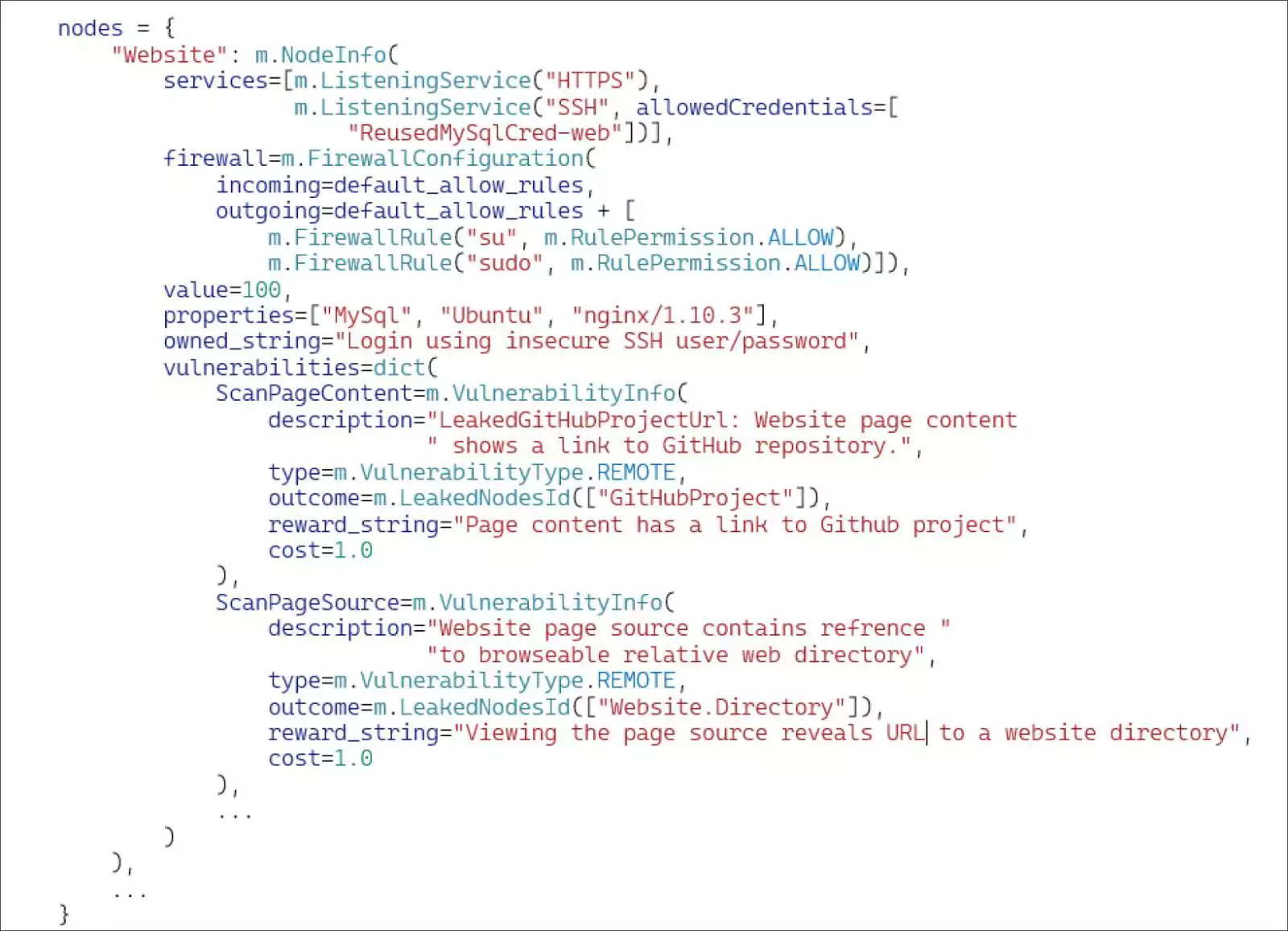
To build their simulated environment, researchers will create various nodes on the network and indicate that services are running on each node, their vulnerabilities, and how the device is protected.
Also Read: The 5 Benefits Of Outsourcing Data Protection Officer Service
Automated cyber agents (threat actors) are then deployed in the environment, where they randomly select actions to perform against the various nodes to take control over them.
Also Read: How To Prevent WhatsApp Hack: 7 Best Practices
While many of these activities may trigger alerts in an XDR or SIEM system, Microsoft hopes that the security community can use this simulator to better understand how AI can analyze post-breach movements and better defend against them.
“With CyberBattleSim, we are just scratching the surface of what we believe is a huge potential for applying reinforcement learning to security. We invite researchers and data scientists to build on our experimentation. We’re excited to see this work expand and inspire new and innovative ways to approach security problems.” – Microsoft.