KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







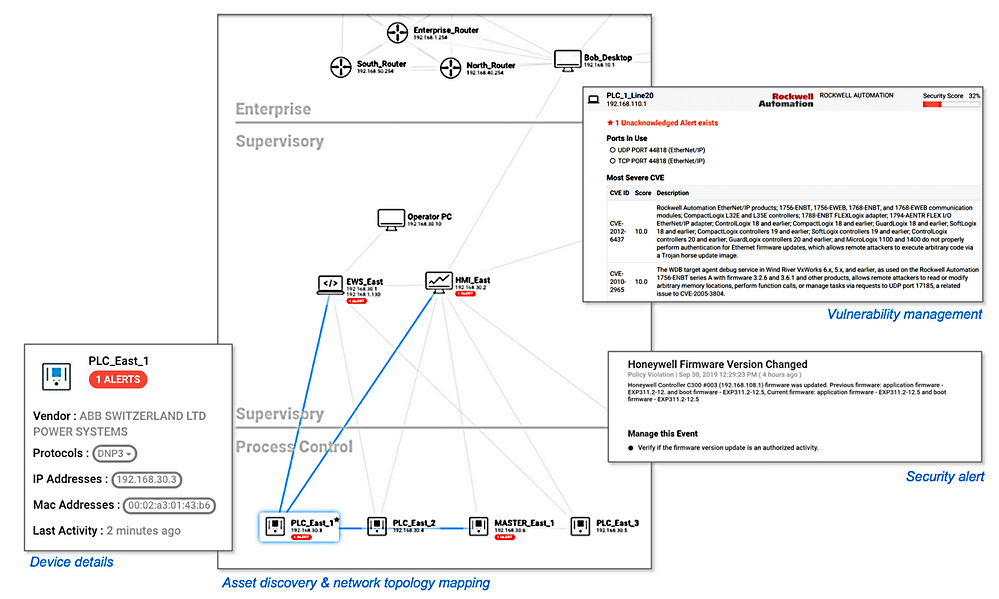
It focuses on providing security monitoring for specialized device types, applications, and machine-to-machine (M2M), as well as specialized industrial protocols (Modbus, DNP3, BACnet, etc.) within IoT/OT environments.
By adding visibility into misconfigured, unmanaged, and unpatched IoT/OT devices, it makes it a lot harder for threat actors to abuse them to gain a foothold into the networks of industrial and critical infrastructure organizations.
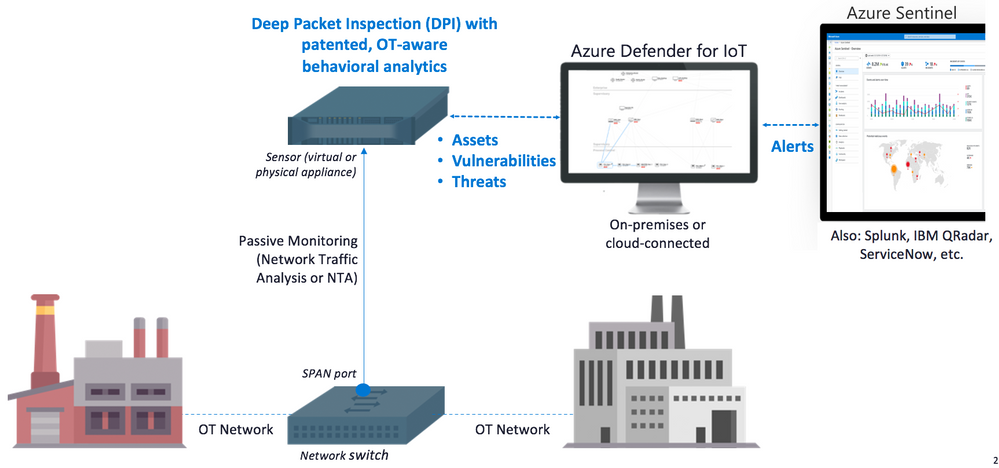
“You can deploy these capabilities fully on-premises without sending any data to Azure,” Phil Neray, Director of Azure IoT Security Strategy, explained.
Also Read: EU GDPR Articles: Key For Business Security And Success
“Or, you can deploy in Azure-connected environments using our new native connector to integrate IoT/OT alerts into Azure Sentinel, benefiting from the scalability and cost benefits of the industry’s first cloud-native SIEM/SOAR platform.”
The alerts sent by Azure Defender for IoT into Azure Sentinel are triggered by analytics detection engines for protocol violation, policy violation, industrial malware detection, anomaly detection, and operational incident detection included on sensors used to collect ICS network traffic.
These alerts are “based on analysis of both real-time and pre-recorded traffic” and they cover a wide range of incidents including but not limited to:
“In addition, you can create custom alerts based on your knowledge of expected device behavior,” according to Microsoft. “An alert acts as an indicator of potential compromise, and should be investigated and remediated.”
Azure Defender for IoT can be tried for free while in public preview, the only requirement being an Azure Defender subscription that is also free of charge for the first 30 days.
You can get started from the IoT Defender Dashboard and you can learn more about how to configure it and its capabilities from here.
Also Read: 7 Simple Tips On How To Create A Good Business Card Data