KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A massive phishing campaign reaching tens of thousands of inboxes impersonated the MacKenzie Bezos-Scott grant foundation promising financial benefits to recipients in exchange of a processing fee.
Known as an “advance fee,” this scam has been practiced since before then internet and became popularized by its “Nigerian prince” variant.
Unlike that version of the scam, though, this campaign benefited by wide distribution and took advantage of the charitable acts last year from author MacKenzie Scott, once married to Amazon founder Jeff Bezos.
Scott announced last December that she had distributed almost $4.2 billion of her fortune to almost 400 organizations in the U.S. dedicated to making a positive social impact.
[subtitle]
Emails impersonating the MacKenzie Bezos-Scott foundation continue to poor in, according to email security platform Ironscales, who says that fraudulent messages reached at least 190,000 mailboxes.
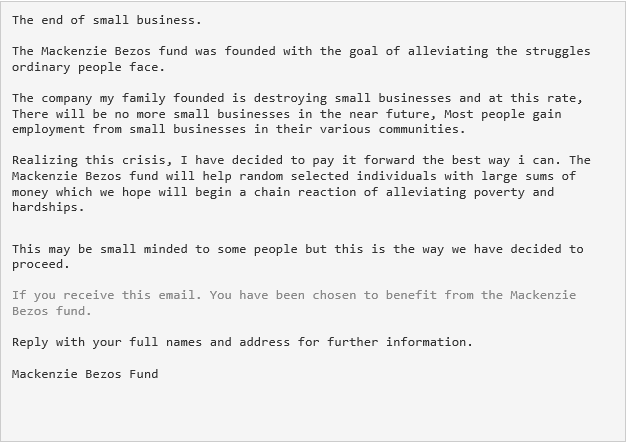
The message purports to be from the charity organization saying that the recipient has been selected to receive a grant.
The alleged funds could be released after replying with some personal details (full name and address) and paying a small processing fee required for the money transfer.
Ironscales believes that the campaign targeted victims that would have reason to believe the messages due to their involvement in the charity sector.
Also Read: The 3 Main Benefits Of PDPA For Your Business
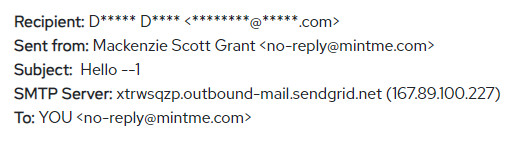
However, this was the only element of complexity. As seen in the screenshot above, there is no challenge in spotting irregularities in the message and looking at the sender’s address reveals the fraud attempt:
Cybercriminals are quick to take advantage of high-profile events such as billions being donated over a few months. They are also aware that some victims may not pay attention to typos and grammar mistakes.
After all, even legitimate messages may contain mistakes or be sufficiently non-descript to raise suspicions. This happened to Rhonda Sanders, the CEO of Arkansas Foodbank.
Also Read: What Do 4 Messaging Apps Get From You? Read The iOS Privacy App Labels
The organization received a MacKenzie Bezos-Scott grant but Sander’s first though was that it was a scam. Nevertheless, she replied to the email and got the good news.