KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







A new ransomware operation named Mount Locker is underway stealing victims’ files before encrypting and then demanding multi-million dollar ransoms.
Starting around the end of July 2020, Mount Locker began breaching corporate networks and deploying their ransomware.
From ransom notes shared with BleepingComputer by victims, the Mount Locker gang is demanding multi-million dollar ransom payments in some cases.
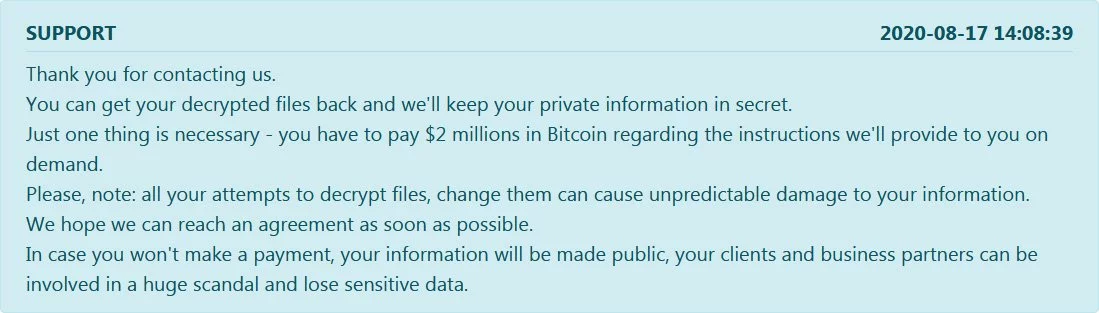
Before encrypting files, Mount Locker will also steal unencrypted files and threaten victims that the data will be published if a ransom is not paid.
Also Read: How To Make A PDPC Complaint: With Its Importance And Impact
For example, Mount Locker told one victim that they stole 400 GB of their data, and if they are not paid, they will contact the victim’s competitors, the media, TV channels, and newspapers.
Ultimately, the victim did not pay, and their data was published to a ransomware data leak site.
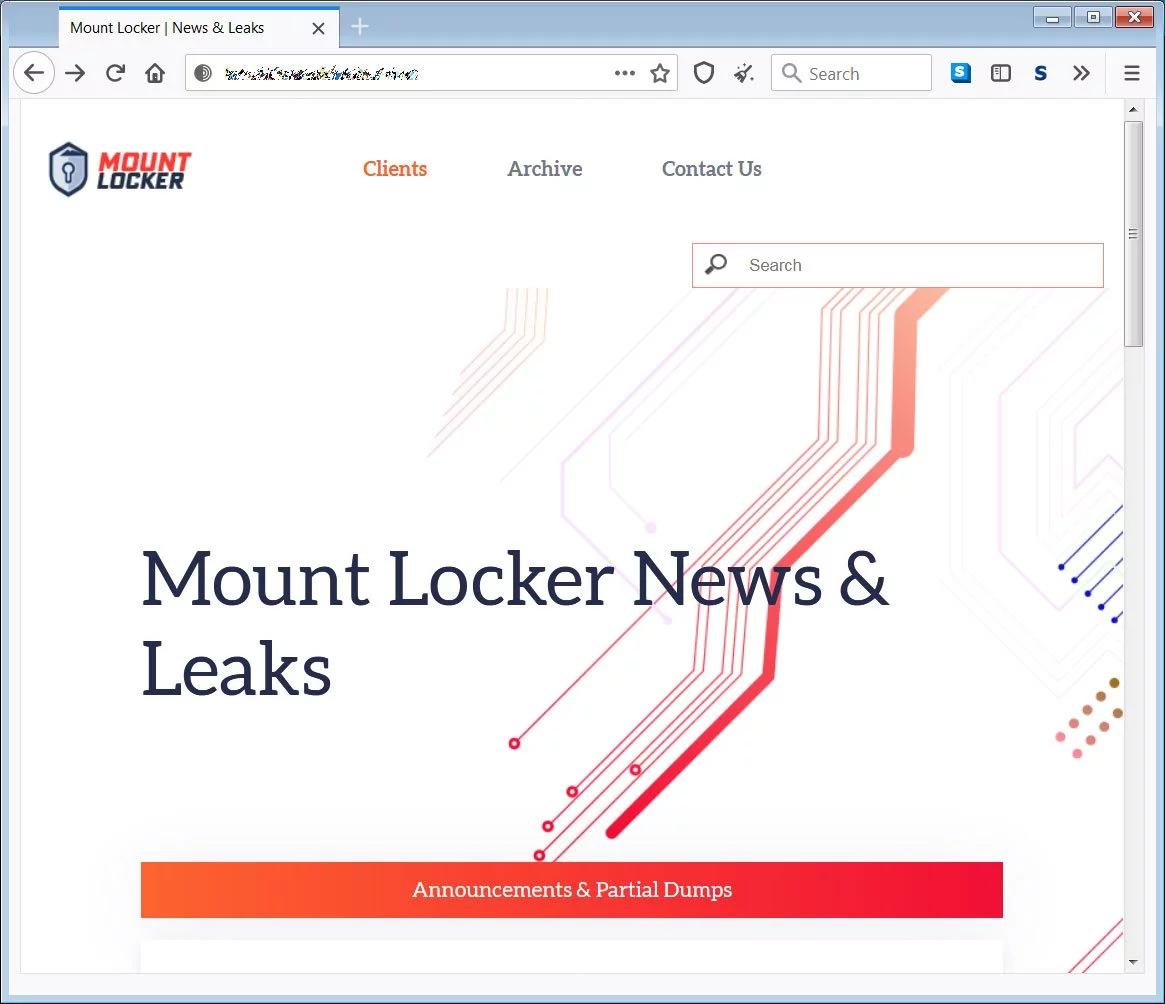
This data leak site currently lists four victims, with only one having files leaked.
It was only until recently that MalwareHunterTeam discovered a sample of Mount Locker, which allow allowed us to get a bit more insight into how the ransomware operates.
Michael Gillespie, who analyzed the ransomware, told BleepingComputer that Mount Locker uses ChaCha20 to encrypt the files and an embedded RSA-2048 public key to encrypt the encryption key.
From our analysis, when encrypting files, the ransomware will add an extension in the format .ReadManual.ID. For example, 1.doc would be encrypted and renamed to 1.doc.ReadManual.C77BFF8C, as shown in the encrypted folder below.
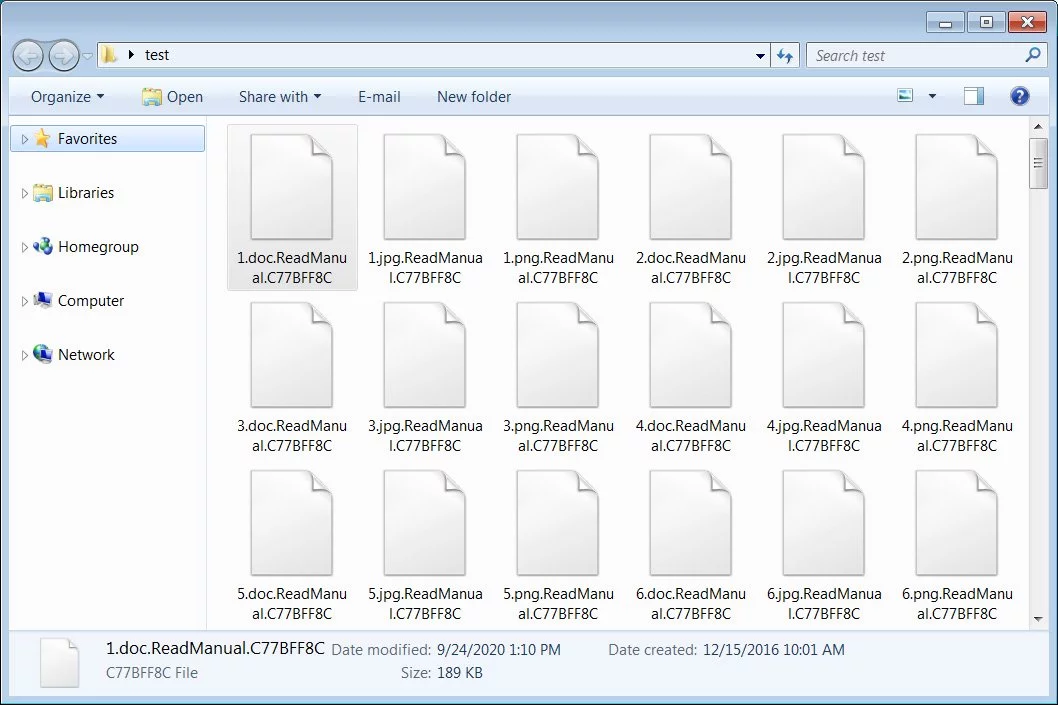
The ransomware will then register the extension in the Registry so that when you click on an encrypted file, it will automatically load the ransom note.
HKCU\Software\Classes\.C77BFF8C\shell\Open\command\ @="explorer.exe RecoveryManual.html"The ransom note is named RecoveryManual.html and contains instructions on how to access the Tor site to communicate with the ransomware operators.
Also Read: 10 Principles On How To Build A Good Governance Model
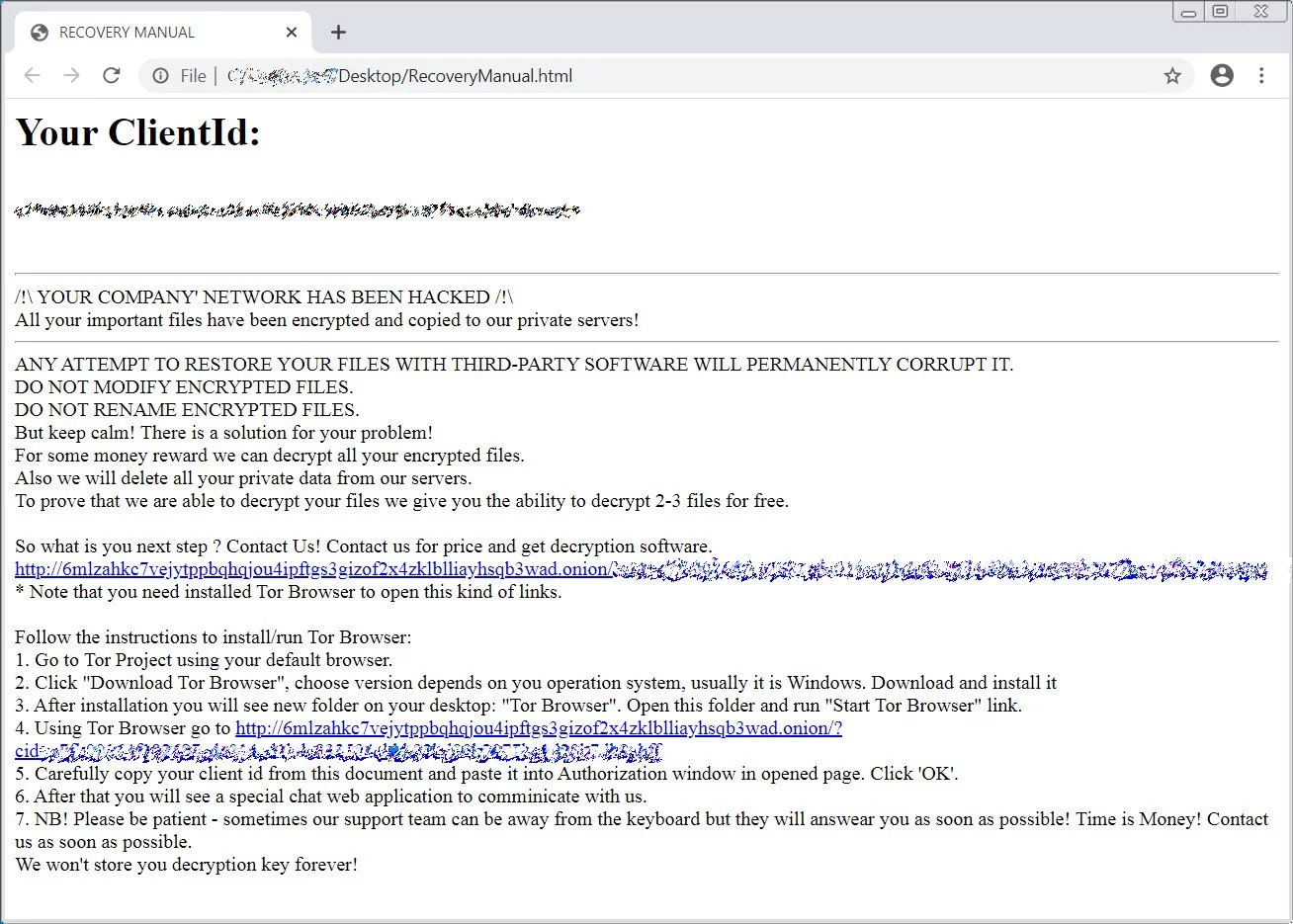
The Tor site is simply a chat service, where victims can negotiate the ransom or ask questions.
Unfortunately, the ransomware is secure, and there is no way to recover your files for free.
For those who wish to receive support related to this ransomware, you can use our dedicated Mount Locker support topic.

Established in 2018, Privacy Ninja is a Singapore-based IT security company specialising in data protection and cybersecurity solutions for businesses. We offer services like vulnerability assessments, penetration testing, and outsourced Data Protection Officer support, helping organisations comply with regulations and safeguard their data.
Singapore
7 Temasek Boulevard,
#12-07, Suntec Tower One,
Singapore 038987
Latest resources sent to your inbox weekly
© 2025 Privacy Ninja. All rights reserved
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!

Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!
