KEEP IN TOUCH
Subscribe to our mailing list to get free tips on Data Protection and Cybersecurity updates weekly!





A ransomware gang who says they stole unencrypted source code for the company’s most popular games and then encrypted CD Projekt’s servers claims to have sold the data.
This past Tuesday, game developer CD Projekt Red disclosed that they suffered a ransomware attack that encrypted devices on their network.
In a ransom note left behind on encrypted systems, the attackers claim to have stolen the source code for Cyberpunk 2077, Witcher 3, Gwent, and an unreleased version of Witcher 3.
The attackers also state that they stole administration, accounting, human resources, and investor relations documents before deploying the ransomware.
Also Read: How To Prevent WhatsApp Hack: 7 Best Practices
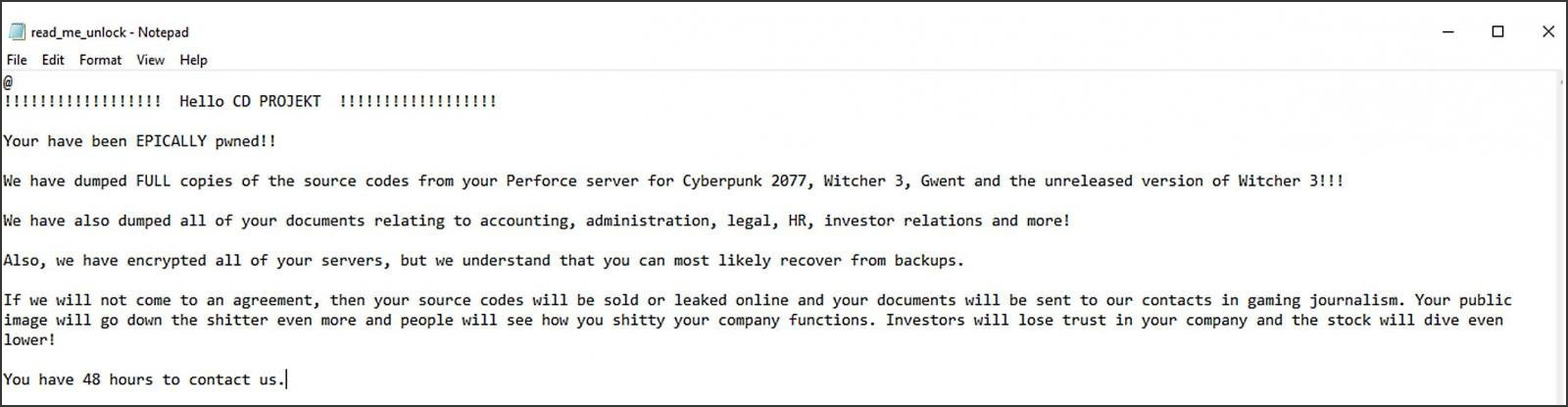
From the company’s ransom note, security researchers were able to determine that the HelloKitty ransomware was used in the attack.
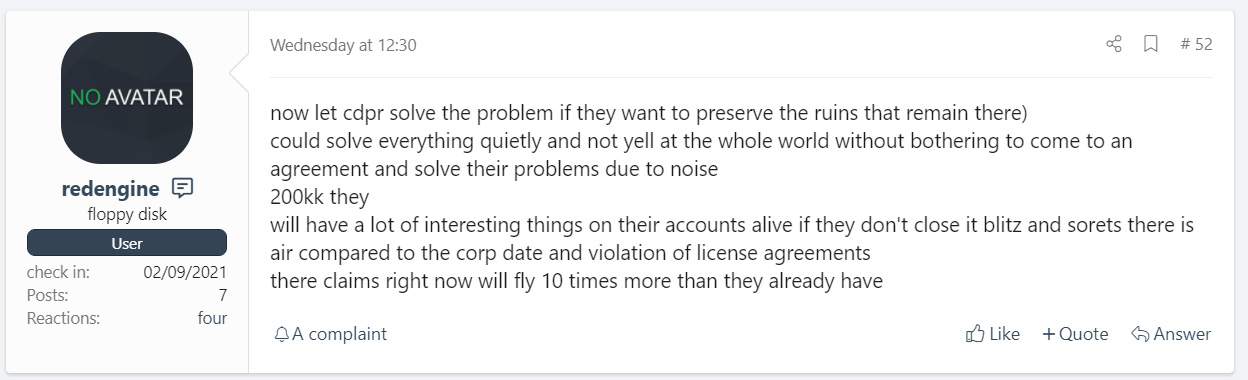
After CD Projekt announced that they would not be paying the ransom, a threat actor named ‘redengine’ created an auction for the stolen data on a hacker forum.
This data allegedly includes the source code for Thonebreaker, Witcher 3, an unreleased Witcher 3 with raytracing, and Cyberpunk 2077. The hackers also state that it would include “dumps of internal documents” and “CD Projekt RED offenses.”
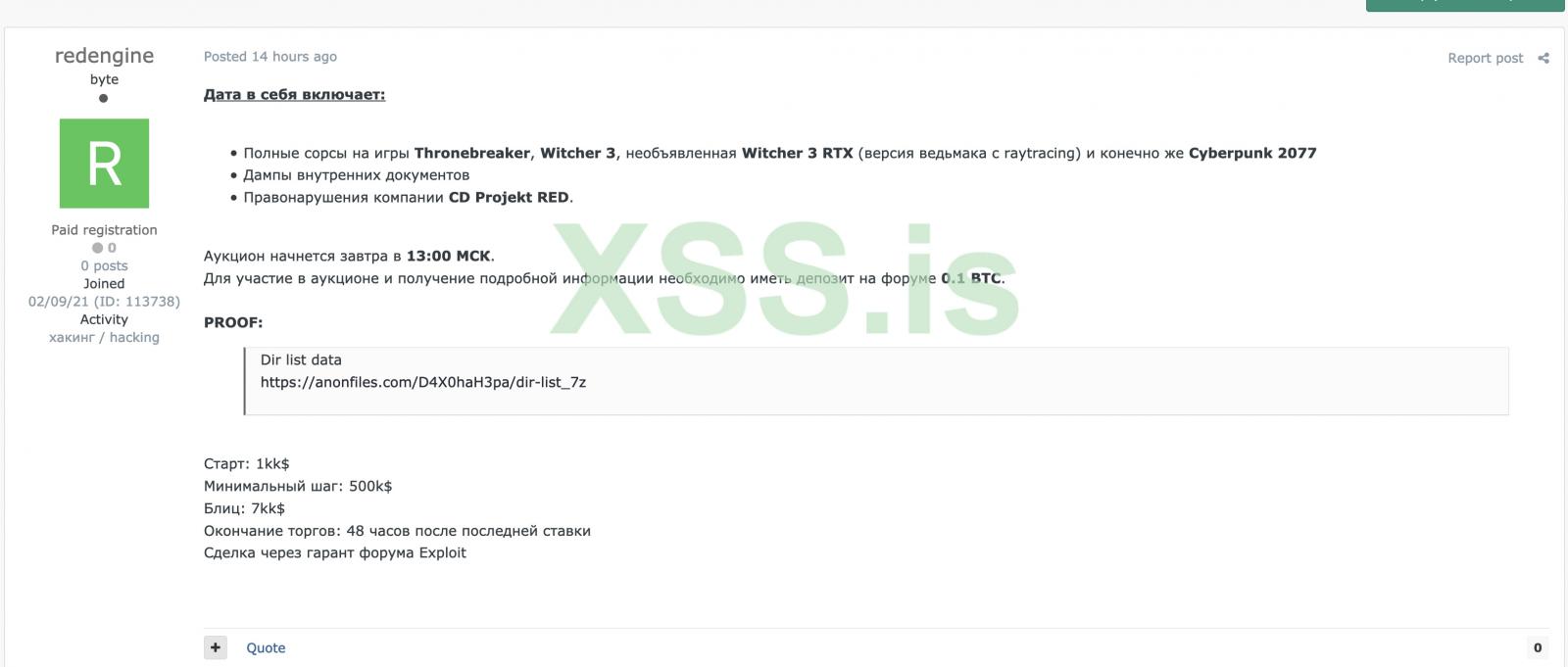
The auction started at $1 million, and bids were in $500,000 increments. For those who wanted to buy it immediately, the threat actors also included a buy now, or blitz, price of $7 million.
The threat actor further posted that the data contains violations that will ruin the reputation of CDPR.
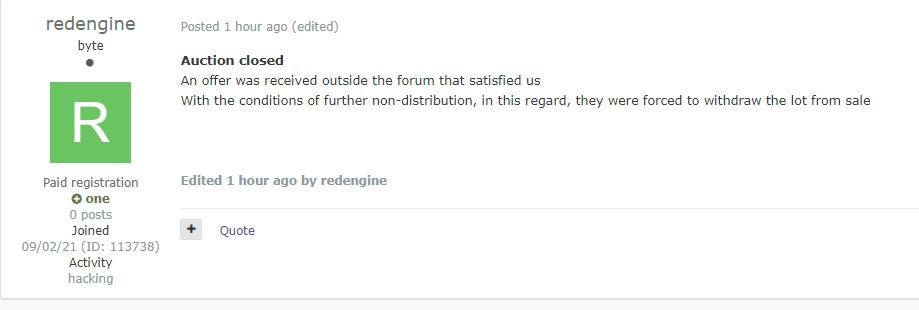
The next day, cybersecurity intelligence company KELA told BleepingComputer that the ransomware gang posted that they sold the data to someone “outside the forum.”
As the terms of the sale required the threat actors to no longer distribute the data, they subsequently closed the auction.
At this time, there is no proof that the threat actors sold the data.
There has been a lot of speculation about who would purchase this data, ranging from competitors wanting to analyze CDPR’s code for corporate secrets to CDPR buying it themselves to hide these secrets.
Some feel it would not make sense for a legitimate software developer to purchase the data due to copyright laws.
Others think the buyer was in fact CD Projekt Red, who purchased it to prevent the source code and internal documents from being released.
Also Read: Going Beyond DPO Meaning: Ever Heard of Outsourced DPO?
The reality is we will likely never know for sure if the data was sold, and if it was, who purchased it.